Researchers at the Ben-Gurion University of the Negev (BGU) Cyber Security Research Center have discovered that virtually any cellphone infected with a malicious code can use GSM phone frequencies to steal critical information from infected “air-gapped” computers.
Air-gapped computers are isolated — separated both logically and physically from public networks — ostensibly so that they cannot be hacked over the Internet or within company networks.
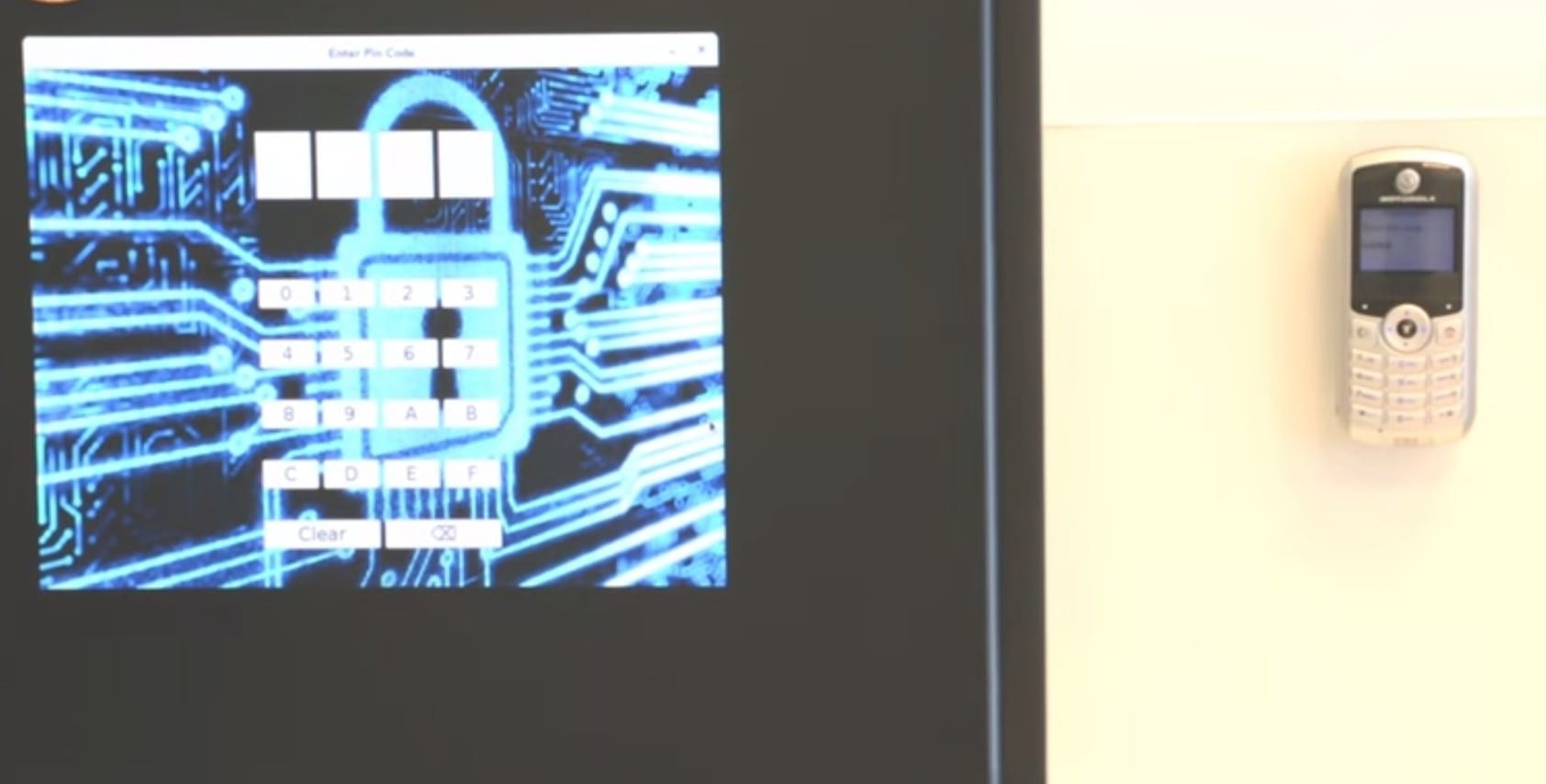
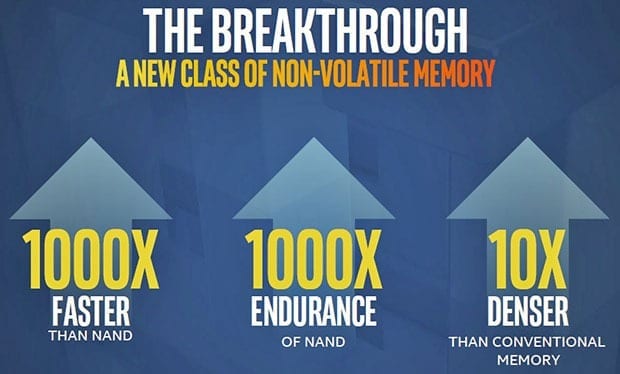
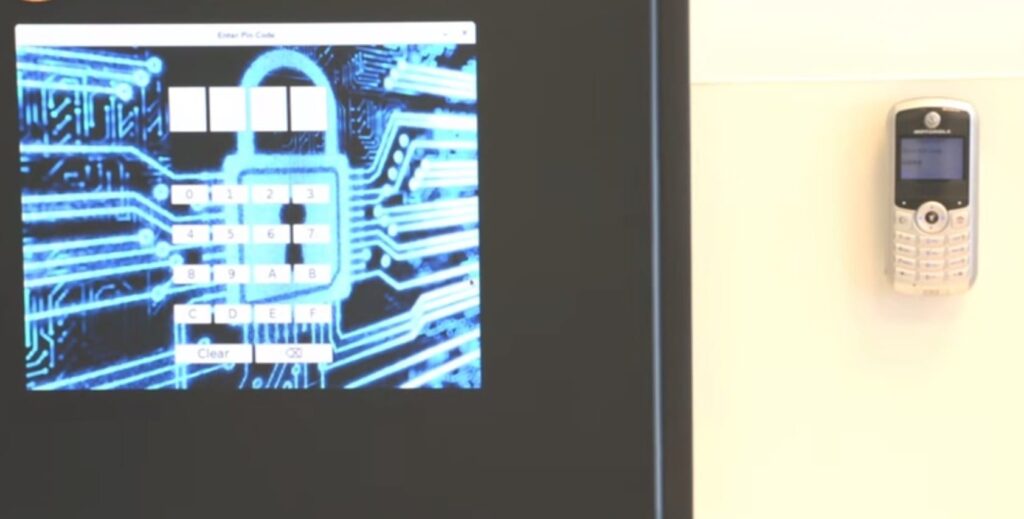
Led by BGU Ph.D. student Mordechai Guri, the research team discovered how to turn an ordinary air-gapped computer into a cellular transmitting antenna using software that modifies the CPU firmware. GSMem malicious software uses the electromagnetic waves from phones to receive and exfiltrate small bits of data, such as security keys and passwords.
Click here to watch a video of the demonstration.
“GSMem takes the air out of the gap and will force the world to rethink air-gap security,” says
Dudu Mimran, chief technology officer of BGU’s Cyber Security Research Center. “Our GSMem malicious software on Windows and Linux has a tiny computational footprint, which makes it very hard to detect. Furthermore, with a dedicated receiver, we were successful exfiltrating data as far as 90 ft. (30 meters) in distance from the computer.”
According to Guri, “Many companies already restrict the use of cell phones or limit the capabilities (no camera, video or Wi-Fi on cell phones) around air-gapped computers. However, phones are often otherwise allowed in the vicinity of air-gapped computers thought to be secure. Since modern computers emit some electromagnetic radiation (EMR) at various wavelengths and strengths, and cellular phones easily receive them, this creates an opportunity for attackers.”
The researchers recommend that countermeasures to mitigate the issue use the “Zone” approach: defined areas or zones around these computers where mobile phones and simple devices are prohibited. Insulation of partition walls may help to mitigate signal reception distance growth if a dedicated hardware receiver is used. Additionally, anomaly detection and behavioral dynamic analysis may help.
Read more: Cellphones Can Steal Data from Computers
The Latest on: Air gapped computers
[google_news title=”” keyword=”Air gapped computers” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]
via Google News
The Latest on: Air gapped computers
- 2024 iPad Air and iPad Pro: 6 Big Missing Featureson May 9, 2024 at 1:00 pm
Apple's latest iPad Air and iPad Pro are thin and light, but a handful of needed features and upgrades are nowhere to be found.
- New Study May Reveal Why Venus Has Almost No Wateron May 8, 2024 at 5:00 pm
The new study fills in a big gap in what the researchers call “the water story on Venus.” Using computer simulations ... where all the water is trapped in the air, you’d wind up with only 3 ...
- iPad Pro M4 vs. MacBook Air M3: a harder choice than everon May 8, 2024 at 12:51 pm
As the iPad Pro becomes more like a MacBook, the comparison between these devices continues to get more interesting.
- MacBook Air M3 13-inch vs. iPad Pro M4: Is Apple's new tablet more powerful?on May 8, 2024 at 9:00 am
The iPad Pro features a "studio-quality four-mic array," while the 13-inch MacBook Air only has a "three-mic array with directional beamforming." iPads used to be limited in terms of apps compared to ...
- Microsoft launches AI chatbot for spieson May 7, 2024 at 12:22 pm
GPT-4 can power AI assistants that converse in a human-like manner. Microsoft has a license to use the technology as part of a deal in exchange for large investments it has made in OpenAI. According ...
- New iPad Pros are the thinnest Apple device ever, feature dual-OLED screenson May 7, 2024 at 7:25 am
Apple's newest iPad Pro, available TK, puts an M TK chip inside a thinner frame available in new 11-inch and 13-inch and sizes, while also upgrading the screens on both to two "tandem" OLED displays ...
- Hackers can steal data by messing with a computer's processoron May 7, 2024 at 6:23 am
Software that has been blocked from connecting to the internet should be secure from hacking attempts, but now researchers have found a way to sneak data out by varying the speed of the computer's pro ...
- Microsoft deploys air-gapped AI for classified defense, intelligence customerson May 7, 2024 at 5:59 am
Microsoft will announce later today the availability of GPT-4 in the Azure Government Top Secret cloud. The tech giant has been working for about 18 months on this effort, which includes the ...
- Venus has almost no water: A new study may reveal whyon May 6, 2024 at 12:55 pm
Billions of years ago, Venus may have harbored as much water as Earth. Today, almost all of it has disappeared. A new study may help to explain why.
- Survey: Air Travel Most Popular Way To Go On Holidays For Swisson May 2, 2024 at 12:03 pm
Despite the climate crisis, flying is the most popular mode of transport to head on holidays – particularly for young, urban and high-income travell ...
via Bing News