Artificial intelligence (AI) research has explored a variety of problems and approaches since its inception, but for the last 20 years or so has been focused on the problems surrounding the... Read more
The tool leverages this technology to detect security-specific properties within a hardware system. For example, the tool can make sure that a cryptographic key does not leak outside a chip’... Read more
“The true significance of this security approach is its potential proactive defense capability. Conventional security systems scan for known attack patterns, which is reactive. Our ano... Read more
If only computers themselves were smart enough to fight off malevolent hackers. That is the premise of an ambitious two-year contest with a $2 million first prize, posed to the world’s compu... Read more
Computer security: Spam in the fridge “THE internet of things” is one of the buzziest bits of jargon around in consumer electronics. The idea is to put computers in all kinds of products—tel... Read more
Stung by revelations of ubiquitous surveillance and compromised software, the internet’s engineers and programmers ponder how to fight back SECURITY guards (at least the good ones) are paid... Read more
Researchers have shown that it is possible to compromise the functioning of a cryptographic chip without changing its physical layout. Based on altering the distribution of dopants in a few... Read more
There’s nothing like attendance at the annual Black Hat and Def Con security/hacker conferences to hike your paranoia into the red zone and keep it there forever. You come away with the sens... Read more
Computer science researchers have programmed a computer to play the game Concentration (also known as Memory). The work could help improve computer security – and improve our understanding o... Read more
Deetectee Microsystems Inc. has invented the first and only technology that enables secure, digital identification of a person in a mobile environment. The invention of Single Burst Optical... Read more
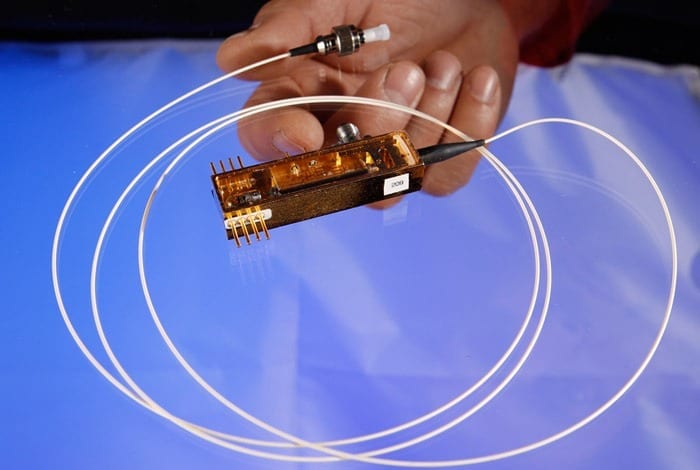
LANL’s quantum cryptography team successfully completed the first-ever demonstration of securing control data for electric grids using quantum cryptography. Recently a Los Alamos Natio... Read more
The whole setup is a low-budget alternative to costly computer graphics CyberCity takes up a mere 48 square feet, but it has a working electric grid, transportation system, and banking netwo... Read more