Could result in a sea change in how to secure computations
New research to be presented at the 18th European Symposium on Research in Computer Security (ESORICS 2013) this week could result in a sea change in how to secure computations.
The collaborative work between the University of Bristol and Aarhus University (Denmark) will be presented by Bristol PhD student Peter Scholl from the Department of Computer Science.
The paper, entitled Practical covertly secure MPC for dishonest majority – or: Breaking the SPDZ limits, builds upon earlier joint work between Bristol and Aarhus and fills in the missing pieces of the jigsaw from the groups prior work that was presented at the CRYPTO conference in Santa Barbara last year.
The SPDZ protocol (pronounced “Speedz”) is a co-development between Bristol and Aarhus and provides the fastest protocol known to implement a theoretical idea called “Multi-Party Computation”.
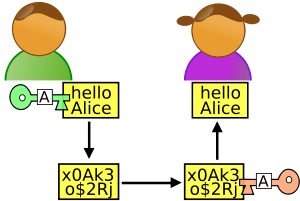
The idea behind Multi-Party Computation is that it should enable two or more people to compute any function of their choosing on their secret inputs, without revealing their inputs to either party. One example is an election, voters want their vote to be counted but they do not want their vote made public.
The protocol developed by the universities turns Multi-Party Computation from a theoretical tool into a practical reality. Using the SPDZ protocol the team can now compute complex functions in a secure manner, enabling possible applications in the finance, drugs and chemical industries where computation often needs to be performed on secret data.
Nigel Smart, Professor of Cryptology in the University of Bristol’s Department of Computer Science and leader on the project, said: “We have demonstrated our protocol to various groups and organisations across the world, and everyone is impressed by how fast we can actually perform secure computations.
The Latest Bing News on:
Cryptography
- Canada's 2 Intelligence Unit: Banker by day, spy by nighton May 18, 2024 at 3:01 am
Honorary Lieutenant-Colonel Don Stewart is the treasurer of the 2 Intelligence Company Senate. He says today’s reservists come from all walks of life — teachers, lawyers, accountants, students, ...
- Apple's New iMessage, Signal, and Post-Quantum Cryptographyon May 17, 2024 at 8:03 am
Message has been updated with cryptography to secure against quantum computers. Understand what this means for privacy and confidentiality.
- Quantum Cryptography Solutions Market to Surge, Predicted to Reach USD 947.63 Million by 2028 with a Thriving 38.28% CAGRon May 17, 2024 at 6:07 am
The "Global Quantum Cryptography Solutions Market 2024-2028" report has been added to ResearchAndMarkets.com's offering. The global quantum cryptography solutions market is poised for significant ...
- Worldcoin Foundation Introduces SMPC System, Deletes Old Iris Codeson May 16, 2024 at 3:35 pm
Applied research from the Worldcoin Foundation and TACEO, a team of cryptography engineers, has advanced the biometric template protection.
- New research to make digital transactions quantum safe and 20 times fasteron May 16, 2024 at 10:42 am
A team of experts, including Monash University researchers, has developed a new technique to implement quantum-safe digital signatures twenty times faster, resulting in speedier and safer online ...
- RSAC Cryptographers' Panel Tackles AI, Post-Quantum, Privacyon May 15, 2024 at 11:46 am
This year's panel, moderated by public key cryptography pioneer Whitfield Diffie, touched on everything from the safe use of artificial intelligence and the adversarial risk it poses to how to secure ...
- Thiel-Backed Cryptography Startup Lagrange Raises $13Mon May 8, 2024 at 6:00 am
Peter Thiel's Founders Fund led a $13.2 million seed funding round into Lagrange Labs, a cryptography startup based on Ethereum's EigenLayer restaking platform.Lagrange specializes in zero-knowledge ...
- Swiss startup unveils post-quantum cryptography library for devson May 8, 2024 at 5:00 am
Swiss startup Terra Quantum has released an open-source repository for quantum-resistant encryption algorithms.
- Future Proof Encryption: Embracing Post-Quantum Cryptography For Quantum-Resilient Solutionson May 7, 2024 at 5:45 am
Let's look at how computing technology could challenge today's encryption protocols and the potential ways to secure ourselves.
- Quantum Cryptography Market Innovative Strategies for Harnessing Future Market Size Growthon May 2, 2024 at 2:11 am
The “Global Quantum Cryptography Market 2024“ research describes the competitive market environment based on production volume, profits, and sales. The report covers even the supply chain analysis of ...
The Latest Google Headlines on:
Cryptography
[google_news title=”” keyword=”cryptography” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]
The Latest Bing News on:
Secure computing
- Akamai (AKAM) Partners EZDRM to Expand Computing Programon May 17, 2024 at 10:17 am
Akamai Technologies Inc. AKAM recently announced that EZDRM Inc. has opted to join the Akamai Qualified Compute Partner Program. The program allows its technology partners to operate their ...
- Bizarre device uses 'blind quantum computing' to let you access quantum computers from homeon May 17, 2024 at 4:00 am
Quantum computers historically required massive amounts of space, but a new system will allow home users to access quantum computers via the cloud.
- Akamai’s cloud computing play gains momentumon May 16, 2024 at 7:05 pm
The company’s compute business could eventually account for the majority of its revenues, surpassing its security and content delivery businesses, says its CEO Tom Leighton ...
- Power/Performance Costs In Chip Securityon May 16, 2024 at 12:01 am
Implementing security measures isn't free. It affects everything from latency and battery life to the equipment and processes used to develop a chip.
- Cloud Security Needs Solutions, Not More Alertson May 15, 2024 at 4:15 am
Cloud security providers can effectively reduce the need for manual work, decrease the overall number of security issues and ultimately make fixes easier.
- Project Hosts' Chief Information Security Officer has Been Appointed to the Federal Secure Cloud Advisory Committeeon May 14, 2024 at 5:00 pm
Palo Alto, CA May 15, 2024 --( PR.com)-- Project Hosts, Inc., a leader in cloud-computing services for secure environments, is pleased to announce the appointment of its Chief Information Security ...
- SEALQ Quantum Computing and IoT: A Transformative Synergy with Next-Generation Root of Trust IoTon May 14, 2024 at 7:36 am
Logistics: In logistics and supply chain management, quantum IoT can optimize routes and inventory management, enhancing efficiency and reducing costs. This means faster delivery times, reduced fuel ...
- Defense In Depth Must Be Part Of Any Quantum Security Conversationon May 13, 2024 at 5:00 am
Without a quantum-based QKD security defense, we will be defending ourselves with a single-point-of-failure approach, and that just is not good enough.
- 5 Best Practices to Secure Your Azure Resourceson May 13, 2024 at 4:37 am
Learn best practices for securing Azure resources to ensure that your cloud infrastructure is fortified against increasingly sophisticated cyber threats.
- A beginner's guide to Google Cloud Platform, the pay-as-you-go cloud computing services vendor with a free tieron May 12, 2024 at 7:52 pm
Google Cloud Platform offers cloud computing resources — with a free tier — to businesses that need servers, computing power, and storage space.
The Latest Google Headlines on:
Secure computing
[google_news title=”” keyword=”secure computing” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]