Until recently, security was a backwater in the world of computing.
Many people cite Albert Einstein’s aphorism “Everything should be made as simple as possible, but no simpler.” Only a handful, however, have had the opportunity to discuss the concept with the physicist over breakfast.
One of those is Peter G. Neumann, now an 80-year-old computer scientist at SRI International, a pioneering engineering research laboratory here.
As an applied-mathematics student at Harvard, Dr. Neumann had a two-hour breakfast with Einstein on Nov. 8, 1952. What the young math student took away was a deeply held philosophy of design that has remained with him for six decades and has been his governing principle of computing and computer security.
For many of those years, Dr. Neumann (pronounced NOY-man) has remained a voice in the wilderness, tirelessly pointing out that the computer industry has a penchant for repeating the mistakes of the past. He has long been one of the nation’s leading specialists in computer security, and early on he predicted that the security flaws that have accompanied the pell-mell explosion of the computer and Internet industries would have disastrous consequences.
“His biggest contribution is to stress the ‘systems’ nature of the security and reliability problems,” said Steven M. Bellovin, chief technology officer of the Federal Trade Commission. “That is, trouble occurs not because of one failure, but because of the way many different pieces interact.”
Dr. Bellovin said that it was Dr. Neumann who originally gave him the insight that “complex systems break in complex ways” — that the increasing complexity of modern hardware and software has made it virtually impossible to identify the flaws and vulnerabilities in computer systems and ensure that they are secure and trustworthy.
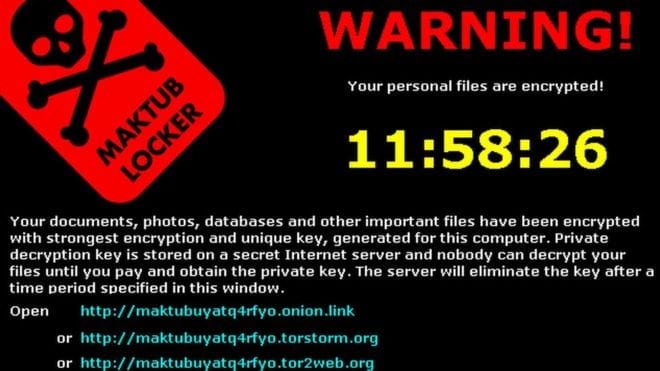
The consequence has come to pass in the form of an epidemic of computer malware and rising concerns about cyberwarfare as a threat to global security, voiced alarmingly this month by the defense secretary, Leon E. Panetta, who warned of a possible “cyber-Pearl Harbor” attack on the United States.
It is remarkable, then, that years after most of his contemporaries have retired, Dr. Neumann is still at it and has seized the opportunity to start over and redesign computers and software from a “clean slate.”
He is leading a team of researchers in an effort to completely rethink how to make computers and networks secure, in a five-year project financed by the Pentagon’s Defense Advanced Research Projects Agency, or Darpa, with Robert N. Watson, a computer security researcher at Cambridge University’s Computer Laboratory.
“I’ve been tilting at the same windmills for basically 40 years,” said Dr. Neumann recently during a lunchtime interview at a Chinese restaurant near his art-filled home in Palo Alto, Calif. “And I get the impression that most of the folks who are responsible don’t want to hear about complexity. They are interested in quick and dirty solutions.”
This might be of interest also: Cyberwarfare statistics: A decade of geopolitical attacks
Go deeper with Bing News on:
Computer security
- Massive Dell data breach hits 49 million users; what this means for your privacy and security
Computer maker Dell faced a huge security challenge after a cyberattack stole information for approximately 49 million customers. Dell confirmed that the type of information stolen includes people’s ...
- Careers In Cybersecurity: Which One Is Right For You?
Education Needed: Bachelor’s degree in computer science, cybersecurity, or a related field like information security or information technology (IT) Career Overview: Cybersecurity engineers asses ...
- Students master computer security essentials at 17th UB Lockdown competition
The completely student-run competition provides a hands-on opportunity for participants to learn the computer security challenges that businesses and organizations face every day. Since 2016, students ...
- 5 Must-Have Security Tools for Your Computer
But with so much advice and so many different options available, what are the must-have security tools for every computer? VPNs . Virtual private networks (VPNs) do much more than ...
- How Computer Vision Is Transforming Cybersecurity
Surveillance and threat detection represent one of the most promising domains where computer vision is making significant strides in cybersecurity. Traditional security measures often rely on ...
Go deeper with Google Headlines on:
Computer security
[google_news title=”” keyword=”computer security” num_posts=”5″ blurb_length=”0″ show_thumb=”left”]
Go deeper with Bing News on:
Cybersecurity
- The British University in Dubai launches Bachelor of Science in Computer Science - Cybersecurity
Through the programme students will develop the capacity to utilise state-of-the-art AI technologies to enhance Cybersecurity ...
- AI, Absenteeism, Cybersecurity, and More at the Tech & Learning Regional Leadership Summit in New England
Forward-thinking educators collaborated during a day of information sharing, fact finding, and a bit of entertainment at the Tech & Learning Summit in Boston.
- ASO ROCK WATCH: As Tinubu suspends cybersecurity levy. One other talking point
President Bola Tinubu suspended the controversial 0.5% cybersecurity levy on electronic banking transactions. One other story from the seat of power, Aso Rock villa, was tracked for your reading ...
- CBN Finally Takes Action After FG Withdraws Cybersecurity Levy
The Central Bank of Nigeria (CBN) has removed the contentious 0.5% cybersecurity fee that banks were mandated to charge on electronic transactions.
- CBN Bows to Pressure, Halts Implementation of Controversial Cybersecurity Levy
CBN has withdrawn controversial circular on 0.5% cybersecurity levy, citing legal concerns and public backlash against the cybercrime levy implementation.
Go deeper with Google Headlines on:
Cybersecurity
[google_news title=”” keyword=”cybersecurity” num_posts=”5″ blurb_length=”0″ show_thumb=”left”]