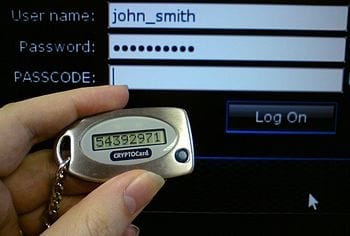
Passwords are a common security measure to protect personal information, but they don’t always prevent hackers from finding a way into devices.
Researchers from the University of Alabama at Birmingham are working to perfect an easy-to-use, secure login protection that eliminates the need to use a password — known as zero-interaction authentication.
Zero-interaction authentication enables a user to access a terminal, such as a laptop or a car, without interacting with the device. Access is granted when the verifying system can detect the user’s security token — such as a mobile phone or a car key — using an authentication protocol over a short-range, wireless communication channel, such as Bluetooth. It eliminates the need for a password and diminishes the security risks that accompany them.
Read more . . .
The Latest on: Zero-interaction authentication
[google_news title=”” keyword=”Zero-interaction authentication” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]
via Google News
The Latest on: Zero-interaction authentication
- Security budgets are growing, but so is vendor sprawlon April 27, 2024 at 11:45 am
It’s estimated that firms on average have between 60 and 75 security tools installed. Although leading vendors logically market the benefits of addressing tools sprawl and complexity through ...
- Entrust fights deepfakes, phishing, and account takeover attacks with AI-powered identity-centric security solutionon April 26, 2024 at 6:14 pm
E ntrust has launched a single-vendor enhanced authentication solution that integrates identity verification (IDV) and identity and access management (IAM). The aim is to fight deepfakes, phishing, ...
- The Impact of Cloud Computing on Zero Trust Network Adoption and Implementationon April 26, 2024 at 2:36 am
Meanwhile, zero-trust network security strengthens defenses against cyber threats by being suspicious of every interaction, whether inside ... Instead, constant authentication of identity and ...
- RBI’s call to replace two-factor authentication requires a multi-layered security approachon April 25, 2024 at 7:45 am
SMS 2FA is vulnerable to exploitation through social engineering. And with the evolution of AI technology, the threats are growing.
- New Brokewell malware takes over Android devices, steals dataon April 25, 2024 at 3:00 am
Security researchers have discovered a new Android banking trojan they named Brokewell that can capture every event on the device, from touches and information displayed to text input and the ...
- Entrust announces integrated identity authentication solutionon April 23, 2024 at 9:20 am
Building on the Onfido acquisition, Entrust can now combine AI-powered biometrics and global Identity Verification with Identity & Access Management.
- Protocol Village: Alchemy Launches 'Pipelines' to Streamline How Blockchain Engineers Extract Dataon April 19, 2024 at 3:50 pm
Telos Foundation, which supports the Telos blockchain, said it will work with Ponos Technology, a zero-knowledge-proof research and development firm, to develop an end-to-end optimized, ...
- Best free CRM in 2024on April 16, 2024 at 4:43 am
Bitrix24: Most flexible for sales and marketing management. Agile CRM: Top-rated customer engagement tools. Freshsales: Excellent free CRM with calling features. Zoho CRM: Best for automating ...
- Social Security scam is hitting inboxes. Here’s what to watch for.on April 15, 2024 at 4:09 pm
Even if an email address appears to be from the agency, beware. Some scammers will use the words “Social Security” or “SSA” in the actual email address, or misspell those terms, or even use a zero ...
- Are passwordless systems the future of authentication?on April 10, 2024 at 11:33 pm
Emerging threats present an opportunity to proactively address the escalating risk of data breaches, and while unconventional, a passwordless approach may offer a viable solution. Businesses are ...
via Bing News