via Future of Privacy Forum
Researchers develop cryptographic scheme that completely hides your personal information from third parties when using single sign-on systems.
Single sign-on systems (SSOs) allow us to login to multiple websites and applications using a single username and password combination. But these are third party systems usually handled by Big Tech companies who have been reported to gather and leak personal information without user consent. Now, researchers from Tokyo University of Science, Japan, have developed a new and secure single sign-on algorithm that eliminates all these problems.
Over the last few decades, as the information era has matured, it has shaped the world of cryptography and made it a varied landscape. Amongst the myriad of encoding methods and cryptosystems currently available for ensuring secure data transfers and user identification, some have become quite popular because of their safety or practicality. For example, if you have ever been given the option to log onto a website using your Facebook or Gmail ID and password, you have encountered a single sign-on (SSO) system at work. The same goes for most smartphones, where signing in with a single username and password combination allows access to many different services and applications.
SSO schemes give users the option to access multiple systems by signing in to just one specific system. This specific system is called the “identity provider” and is regarded as a trusted entity that can verify and store the identity of the user. When the user attempts to access a service via the SSO, the “service provider” asks this identity provider to authenticate the user.
The advantages of SSO systems are many. For one, users need not remember several username and password combinations for each website or application. This translates into fewer people forgetting their passwords and, in turn, fewer telephone calls to IT support centers. Moreover, SSO reduces the hassle of logging in, which can, for example, encourage employees to use their company’s security-oriented tools for tasks such as secure file transfer.
But with these advantages come some grave concerns. SSO systems are often run by Big Tech companies, who have, in the past, been reported to gather people’s personal information from apps and websites (service providers) without their consent, for targeted advertising and other marketing purposes. Some people are also concerned that their ID and password could be stored locally by third parties when they provide them to the SSO mechanism.
In an effort to address these problems, Associate Professor Satoshi Iriyama from Tokyo University of Science and his colleague Dr Maki Kihara have recently developed a new SSO algorithm that on principle prevents such holistic information exchange. In their paper, published in Cryptography, they describe the new algorithm in great detail after going over their motivations for developing it. Dr Iriyama states: “We aimed to develop an SSO algorithm that does not disclose the user’s identity and sensitive personal information to the service provider. In this way, our SSO algorithm uses personal information only for authentication of the user, as originally intended when SSO systems were introduced.”
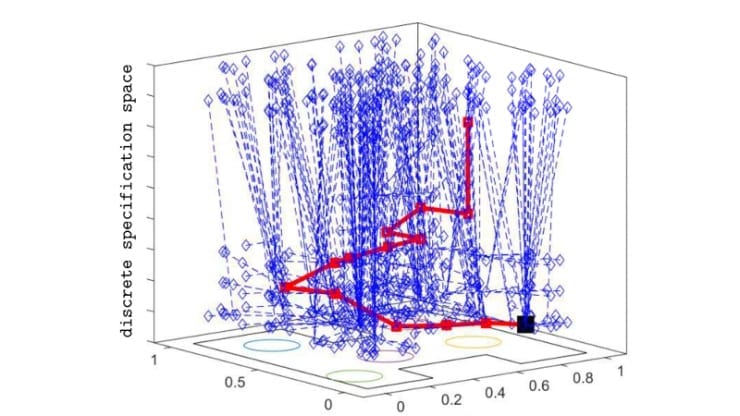
Because of the way this SSO algorithm is designed, it is impossible in essence for user information to be disclosed without authorization. This is achieved, as explained by Dr Iriyama, by applying the principle of “handling information while it is still encrypted.” In their SSO algorithm, all parties exchange encrypted messages but never exchange decryption keys, and no one is ever in possession of all the pieces of the puzzle because no one has the keys to all the information. While the service provider (not the identity provider) gets to know whether a user was successfully authenticated, they do not get access to the user’s identity and any of their sensitive personal information. This in turn breaks the link that allows identity providers to draw specific user information from service providers.
The proposed scheme offers many other advantages. In terms of security, it is impervious by design to all typical forms of attack by which information or passwords are stolen. For instance, as Dr Iriyama explains, “Our algorithm can be used not only with an ID and a password, but also with any other type of identity information, such as biometrics, credit card data, and unique numbers known by the user.” This also means that users can only provide identity information that they wish to disclose, reducing the risk of Big Tech companies or other third parties siphoning off personal information. In addition, the algorithm runs remarkably fast, an essential quality to ensure that the computational burden does not hinder its implementation.
This study will hopefully bring about positive changes in current SSO systems, so that more users are encouraged to use them and reap their many benefits.
The Latest Updates from Bing News & Google News
Go deeper with Bing News on:
Single sign-on system
- Tiger baseball earns hard-fought win at South Knox
The Princeton Community High School baseball team, ranked No. 5 in the IHSBCA Class 3A Poll, continued its busy 2024 season schedule with a road trip to ...
- Serj Tankian Announces New Single 'A.F. Day'
System of a Down's Serj Tankian announced the impending release of his new solo single, "A.F. Day," on April 29. The song, which Tankian wrote during System's early days, will be a part of the ...
- 7 Best Streaming Services for Live TV of May 2024
Looking for the best streaming services for live TV? We have rounded up the best of the best services for streaming live TV, giving you an unbiased, direct review of what you’ll get for your ...
- Researchers just found more than 1,000 new solar system objects hiding in plain sight
Artificial intelligence trained by asteroid-hunting citizen scientists helped identify more than 1,000 never-before-seen solar system objects from old Hubble images spanning two decades.
- 'He made you smile': Single-A Fayetteville pays homage to former prospect
As Single-A Fayetteville assembled for its series opener with Down East on Tuesday, an additional jersey was prepared for the game. This uniform top was never meant to be worn that day, though. It ...
Go deeper with Google Headlines on:
Single sign-on system
[google_news title=”” keyword=”single sign-on system” num_posts=”5″ blurb_length=”0″ show_thumb=”left”]
Go deeper with Bing News on:
Cryptographic scheme
- Marriott admits it falsely claimed for five years it was using encryption during 2018 breach
Marriot revealed in a court case around a massive 2018 data breach that it had been using secure hash algorithm 1 and not the much more secure AES-1 encryption as it had earlier maintained.
- Researchers create verification techniques to increase security in AI and image processing
A team of researchers from the Institute IMDEA Software, Universidad Carlos III de Madrid and NEC Laboratories Europe has introduced a novel framework that promises to improve the efficiency and ...
- Good news, iPad fans – the Delta Nintendo emulator for iOS is coming to iPadOS soon
There's no time frame yet for when Delta for iPadOS will show up, but it shouldn't be too long now. If you live in the EU and you're signed up to the relevant Patreon, you can already download and ...
- Researchers create innovative verification techniques to increase security in artificial intelligence and image processing
At its core is a modular approach to verifiable computation of sequential operations, which is based on a new cryptographic primitive known as VE (Verifiable Evaluation Scheme). The researchers ...
- Q-day approaching: Can Ethereum survive a quantum emergency?
Ethereum seems to have established an emergency protocol to survive if a quantum emergency is detected. However, the emergency solution has serious caveats, which should make the Ethereum developer ...
Go deeper with Google Headlines on:
Cryptographic scheme
[google_news title=”” keyword=”disease” num_posts=”5″ blurb_length=”0″ show_thumb=”left”]