The answer is yes, according to a paper in the SIAM Journal on Discrete Mathematics.
In a paper published in the journal last month, authors Anthony Bonato, Dieter Mitsche, and Pawel Pralat describe a mathematical model to disrupt flow of information in a complex real-world network, such as a terrorist organization, using minimal resources.
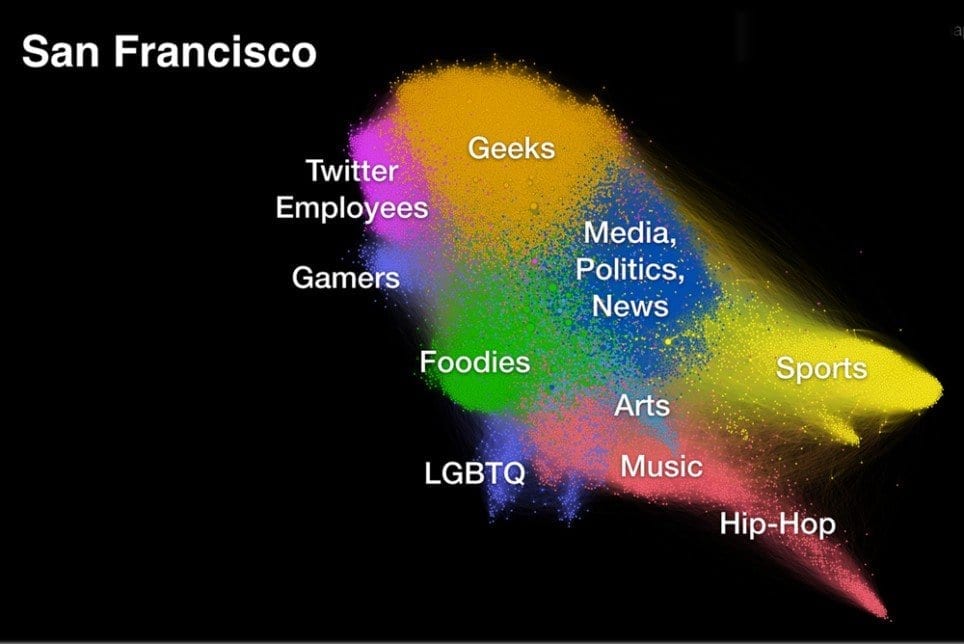
Terror networks are comparable in their structure to hierarchical organization in companies and certain online social networks, where information flows in one direction from a source, which produces the information or data, downwards to sinks, which consume it. Such networks are called hierarchical social networks.
“In such networks, the flow of information is often one way,” explains author Pawel Pralat. “For example, a celebrity such as Justin Bieber sends out a tweet, which is sent to millions of his followers. These followers send out their own retweets, and so on. We may therefore view hierarchical social networks as directed networks without cycles, or directed acyclic graphs (DAGs).”
Here, there is no requirement for reciprocity (the celebrity does not necessarily follow his or her followers). Similarly, in a terrorist network, the leaders pass plans down to the foot soldiers, and usually only one messenger needs to receive the message for the plan to be executed.
Disruption of the flow of information would correspond to halting the spread of news in an online social network or intercepting messages in a terror network.
The authors propose a generalized stochastic model for the flow and disruption of information based on a two-player outdoor game called “Seepage,” where players who depict agents attempt to block the movement of another player, an intruder, from a source node to a sink. “The game—motivated by the 1973 eruption of the Eldfell volcano in Iceland—displays some similarities to an approach used in mathematical counterterrorism, where special kinds of DAGs are used to model the disruption of terrorist cells,” says Pralat.
The motivating eruption caused a major crisis at the time, as lava flow threatened to close off the harbor, the island’s main source of income. In the game, inhabitants attempt to protect the harbor by pouring water on the volcanic lava to halt its progress. A mathematical model of the game pits two opponents against each other—the sludge, or intruder, against the greens, or agents— forming a directed acyclic graph, with one source (the top of the volcano) and many sinks representing the lake. The parameter, “seepage,” represents the amount of contamination, and the “green number” corresponds to the number of agents required to halt it.
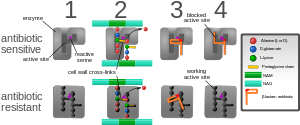
A previous study modeled terrorist cells as partially ordered sets (a special kind of DAG), which are often used in mathematics to analyze an ordering, sequencing, or arrangement of distinct objects. In such a system, terrorist plans are formulated by nodes at the top of the hierarchy, which represent the leaders or maximal nodes of the set. The plans are transmitted down to the nodes at the bottom: these represent foot soldiers in a terror network or minimal nodes in the set who would be presumed to carry out these plans. The assumption is that one messenger is sufficient for reception and execution of the plan. Thus, if the partially ordered set represents a courier network for a terrorist organization, the intention would be to block all routes from the maximal node to the minimal nodes by capturing or killing a subset of agents.
In this paper, the authors utilize the similarities in the previous terrorist cell model to Seepage, where greens try to prevent the sludge from moving to the sinks by blocking nodes. A number of different winning strategies employed by both players are explored when played on a DAG. The seepage and green number for disrupting a given hierarchical social network are analyzed.
The primary difference from the previous study’s model is that the Seepage model is dynamic: greens can move and choose new sets of nodes over time. The authors determine that Seepage is a more realistic model of counterterrorism, as the agents do not necessarily act all at once, but over time.
The Latest Bing News on:
Detect terrorism networks
- Did IDF Lure and Shoot Palestinians Using Drones Playing Recordings of Crying Infants?on April 26, 2024 at 4:54 pm
On April 16, 2024, the outlet Middle East Eye reported on alleged acts of cruelty by the Israeli Defense Forces against residents of Al Nuseirat refugee camp in Gaza involving armed quadcopter drones ...
- Understanding the Corporate Transparency Act (CTA) and Its Possible Impact on Community Associationson April 26, 2024 at 7:02 am
The CTA poses potential challenges for volunteer association board members in private residential communities, who must now provide personal information to FinCEN.
- Lukashenko calls on people to support fight against threats of terrorism, extremismon April 25, 2024 at 6:36 am
Belarusian President and Chairman of the 7th Belarusian People’s Congress Aleksandr Lukashenko appealed to the public for support in the fight against the threats of terrorism and extremism from the ...
- In Australia, seven people arrested in counter-terrorism operationson April 23, 2024 at 12:06 pm
Seven people constituting 'an unacceptable risk and threat” to the Australian population were arrested during anti-terrorist searches which mobilized more News ...
- Nigeria: Tinubu Advocates African Comprehensive Approach to Combating Terrorismon April 23, 2024 at 5:10 am
President Bola Tinubu on Monday, stressed the necessity for Africa to take a comprehensive approach to combating terrorism, not only through might, but by addressing the root causes of the scourge, ...
- Tinubu blames illegal mining for terrorism fundingon April 22, 2024 at 11:01 pm
President Bola Tinubu, on Monday, linked terrorism financing to illegal mining.“Look at the illegal mining that plagues so many of our nations today. Those who think illegal mining has no connection ...
- Corporate Transparency Act Compliance: What Company Owners Need to Know in 2024 (and Beyond)on April 22, 2024 at 4:59 pm
While the U.S. Treasury Department has stated that it intends to use the Corporate Transparency Act to, “disrupt financial anonymity that enables crimes such as corruption, drug trafficking, and ...
- Illegal mining fueling terrorism — Tinubuon April 22, 2024 at 1:31 pm
President Bola Tinubu has stressed that those who think that illegal mining has no connection with financing terrorism are sorely mistaken.He has, therefore, emphasized that while seeking to address ...
- Full Text Of Tinubu’s Speech At African Counter-terrorism Meetingon April 22, 2024 at 9:11 am
President Bola Ahmed Tinubu has called on African leaders to unite and fight terrorism and other threats. He stated this on Monday at the opening of the African high-level meeting on counter-terrorism ...
- Tinubu: External Funding Fuelling Illegal Mining, Terrorism In Africaon April 22, 2024 at 8:59 am
Dedicated to coordinating and implementing counter-terrorism strategies, the NCTC significantly enhances our capacity to detect, prevent ... and disrupt the illicit trafficking networks that fuel ...
The Latest Google Headlines on:
Detect terrorism networks
[google_news title=”” keyword=”detect terrorism networks” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]
The Latest Bing News on:
Terror networks
- Teen facing terror-related charges as part of Sydney church stabbing investigation was already on bail for gun possession chargeson April 26, 2024 at 2:40 pm
The boy, who cannot be named for legal reasons, appeared before the Children's Court in Parramatta on Thursday charged with possessing or controlling extremist material, with the prosecution alleging ...
- Teen facing terror-related charges as part of Wakeley church stabbing investigation was already on conditional bail for gun possession chargeson April 26, 2024 at 2:12 pm
Court documents have revealed a 14-year-old boy charged with terrorism-related offences as part of an investigation in to the Wakeley Church stabbing was on conditional bail for a gun possession ...
- US students fall prey to the terror propagandaon April 26, 2024 at 1:37 pm
Your protests are for brainwashing, for the propaganda of corrupt lobbies inside America. When the symbol of Islamic left (pro regime reformists) entered America and falsely spoke of dialogue of ...
- US, UK, and Canada sanction Iranian drone networkon April 25, 2024 at 4:27 pm
The United States, along with the United Kingdom and Canada, announced additional sanctions targeting Iran's drone proliferation network.
- Ex-Mossad expert warns Iran has built global financial network to bypass sanctionson April 25, 2024 at 2:48 pm
Udi Levy, former head of spy agency’s financial division, says if Israel's partners seriously intend to weaken Tehran, they must target its money-transferring infrastructure The post Ex-Mossad expert ...
- Influential former IS supporter Wassim Fayad drawn into probe of alleged Sydney teen terror networkon April 25, 2024 at 12:55 am
An influential former Islamic State supporter who was released from a supervision order last year was questioned in Wednesday's police raids on an alleged terrorism network involving a group of Sydney ...
- Five Australian Teens Charged Following Anti-terror Raidson April 24, 2024 at 9:48 pm
Five teenagers were charged Thursday following a wave of anti-terror raids across Sydney, as hundreds of police swooped on a network they said posed an "unacceptable risk" to the public.
- First online terror group proscribed in the UKon April 24, 2024 at 11:39 am
Terrorgram will become the sixth extreme right wing terrorist group to be banned in the UK, on the list of 81 banned organisations.
- "Terrorgram": UK Government Cracks Down On Online Terror Network On Telegram Appon April 23, 2024 at 4:21 am
The group, which operates on the messaging app Telegram, has been linked to several deadly attacks around the world and promotes white supremacist ideologies.
- Britain to proscribe Terrorgram collective as terrorist organisationon April 22, 2024 at 3:56 am
Britain said on Monday it would proscribe the Terrorgram collective, an extreme right-wing online network, as a terrorist organisation, meaning it would become a criminal offense in the country to ...
The Latest Google Headlines on:
Terror networks
[google_news title=”” keyword=”Terror networks” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]