Modern cell phones are vulnerable to attacks from rogue cellular transmitters called IMSI-catchers — surveillance devices that can precisely locate mobile phones, eavesdrop on conversations or send spam.
Recent leaks and public records requests have revealed that law enforcement in many U.S. cities have used the surveillance devices to locate suspects or hunt for illegal activity. But despite extensive public debate about their use and privacy implications, little is known about how comprehensively International Mobile Subscriber Identity- (IMSI) catchers — also known as cell-site simulators or Stingrays — are being used by governments, hackers or criminals in any given city.
University of Washington security researchers have developed a new system called SeaGlass to detect anomalies in the cellular landscape that can indicate where and when these surveillance devices are being used. The new system is described in a paper to be published in June 2017 in Proceedings on Privacy Enhancing Technologies.
“Up until now the use of IMSI-catchers around the world has been shrouded in mystery, and this lack of concrete information is a barrier to informed public discussion,” said co-lead author Peter Ney, a doctoral student at the Allen School of Computer Science & Engineering at the UW. “Having additional, independent and credible sources of information on cell-site simulators is critical to understanding how — and how responsibly — they are being used.”
During a two-month deployment in which SeaGlass sensors were installed in 15 ridesharing vehicles in Seattle and Milwaukee, researchers identified dozens of anomalies that were consistent with patterns one might expect from cell-site simulators.
However, researchers cautioned, without corroborating evidence from public records requests or other documentation about where cell-site simulators are being used — or suspicious activity seen over a longer period of time — they cannot definitively say the signals came from IMSI-catchers.
“In this space there’s a lot of speculation, so we want to be careful about our conclusions. We did find weird and interesting patterns at certain locations that match what we would expect to see from a cell-site simulator, but that’s as much as we can say from an initial pilot study,” co-lead author Ian Smith, a former Allen School research scientist. “But we think that SeaGlass is a promising technology that — with wider deployment — can be used to help empower citizens and communities to monitor this type of surveillance.”
Cell-site simulators work by pretending to be a legitimate cell tower that a phone would normally communicate with, and tricking the phone into sending back identifying information about its location and how it is communicating. The portable surveillance devices now range in size from a walkie-talkie to a suitcase, and in price from several thousand to hundreds of thousands of dollars.
Law enforcement teams in the U.S. have used the technology to locate people of interest, to find equipment used in the commission of crimes and even to collect massive amounts of cell phone data from airplanes. Even less is known about how spies or cyber criminals are deploying them worldwide, especially as models become more affordable or able to be built in a hacker’s garage.
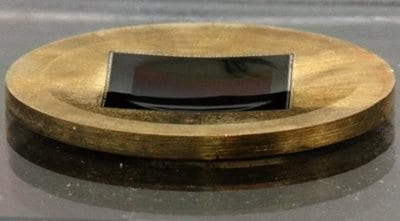
SeaGlass sensors are made with off-the-shelf parts that are packed into a box and installed in a vehicle’s trunk, with antennas placed on or near windows.
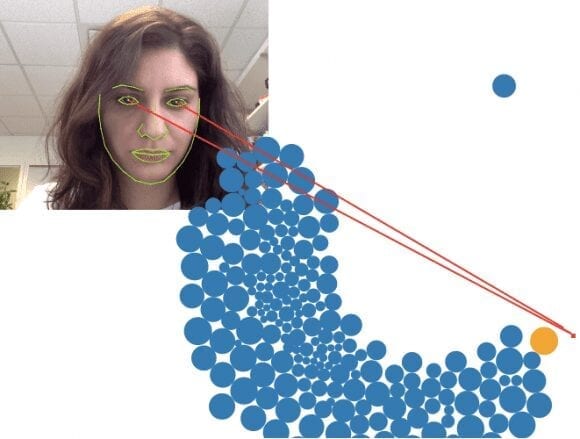
To catch these IMSI-catchers in the act, SeaGlass uses sensors built from off-the-shelf parts that can be installed in vehicles — ideally ones that drive long hours and to many parts of a city, such as ridesharing vehicles or other fleets. The sensors pick up signals broadcast from the existing cell tower network, which remain fairly constant. Then SeaGlass aggregates that data over time to create a baseline map of “normal” cell tower behavior.
The team from the UW Security and Privacy Research Lab developed algorithms and other methods to detect irregularities in the cellular network that can expose the presence of a simulator. These include a strong signal in an odd spot or at an odd frequency that has never been there before, “temporary” towers that disappear after a short time and signal configurations that are different from what a carrier would normally transmit.
Allen School doctoral student and co-author Gabriel Cadamuro built statistical models to help find anomalies in the data. The team’s survey approach differs from existing apps that attempt to detect attacks from a cell-site simulator on an individual’s phone.
“We’re looking at the whole cellular landscape and pinpointing discrepancies in data, while the apps for the most part are guessing at how a cell-site simulator would act with a phone,” said Ney.
Co-author and Allen School professor Tadayoshi Kohno added, “We’ve demonstrated that SeaGlass is effective in detecting these irregularities and narrowing the universe of things people might want to investigate further.”
For instance, around an immigration services building south of Seattle run by the U.S. Department of Homeland Security, SeaGlass detected a cell tower that transmitted on six different frequencies over the two-month period. That was notable because 96 percent of all other base cell towers broadcast on a single channel, and the other 4 percent only used two or three channels.
The team also detected an odd signal near the Seattle-Tacoma International airport with suspicious properties that were markedly different from those normally used by network providers.
Those patterns would make sense if a mimicking cell-site simulator were operating in those areas, the researchers said, but further investigation would be necessary to definitively reach that conclusion.
“This issue is bigger than one team of researchers,” said Smith. “We’re eager to push this out into the community and find partners who can crowdsource.
Learn more: Catching the IMSI-catchers: SeaGlass brings transparency to cell phone surveillance
The Latest Bing News on:
Cell phone surveillance
- Louisville police say little about powerful cell phone hacking toolon May 8, 2024 at 8:42 am
A doorbell camera caught it all.The footage showed three men climbing the stairs to the third floor of an apartment complex in far south Louisville earlier this year. One of the men stooped to snatch ...
- How to prepare your phone for a proteston May 6, 2024 at 12:41 pm
Whatever you’re protesting or counter-protesting, here are some simple steps to take before hitting the streets.
- Barclays issues warning about 'harmful' mobile phone scam that most people don't spoton May 5, 2024 at 1:39 am
Barclays is warning people in the UK to be vigilant of a "harmful" mobile phone malware scam that most people are unaware they're at risk of. The bank's research shows that one in five (21%) consumers ...
- Best Android phone 2024 including Samsung, Google, Nothing and moreon May 2, 2024 at 7:18 pm
In 2024, our favourite iPhone alternatives are the top Pixel phones and the best Samsung phones. But there are countless other brands out there running the Android operating system including Nothing, ...
- Documents tell how video and cell phone data led to arrest in murder of Velma manon May 2, 2024 at 4:02 pm
Investigators used surveillance video to track the truck back to Charlus Terry Bishop’s home. Authorities then obtained cell phone data to place Bishop at the crime scene. Investigators believe the ...
- Why students harmed by addictive social media need more than cellphone bans and surveillanceon May 2, 2024 at 9:06 am
Instead of trying to ban it and monitoring students to make sure they adhere to the ban, schools should focus on improving digital media literacy and critical thinking — for students and their ...
- Don't know what to do with your old phone? Turn it into a home cameraon May 1, 2024 at 8:18 am
Exactly! You can run the Wi-Fi camera yourself using an old smartphone. After all, a mobile phone camera has the same capabilities as factory devices for monitoring your home. For this purpose, you ...
- As Telegram's Popularity Soars, Is It 'A Spy In Every Ukrainian's Pocket'?on May 1, 2024 at 6:20 am
With 72 percent of Ukrainians using it to get news and with some state agencies relying on it, Telegram has become the key social-media platform in wartime Ukraine. Critics accuse it of facilitating ...
- Parma City School District bans cell phone use as Ohio legislators weigh similar statewide billon April 30, 2024 at 9:01 pm
Smialek tells 3News cell phones have become a big distraction in the classroom, and a way for students to interact without anyone monitoring. According to him, administrators have seen kids use phones ...
- The Best Free Spy Apps in 2024 Testedon April 30, 2024 at 4:55 am
The best free spy apps allow you to remotely monitor and even control a target's device, be it an Android or iPhone, at little to no cost.
The Latest Google Headlines on:
Cell phone surveillance
[google_news title=”” keyword=”cell phone surveillance” num_posts=”10″ blurb_length=”0″ show_thumb=”left”] [/vc_column_text]The Latest Bing News on:
Surveillance devices
- AI surveillance is on the horizon, but Mullvad VPN might have a fixon May 9, 2024 at 9:55 am
Mass surveillance is a huge problem for VPNs—even more so following the AI revolution. That's why Mullvad is boosting its protection with DAITA.
- Russia builds surveillance bases near northern Japan. Is it ‘punishing’ Tokyo for supporting Ukraine?on May 8, 2024 at 9:00 pm
Russia's new development on the Kuril Islands aims to 'punish' Japan for supporting international sanctions and providing aid to Ukraine, analysts say The new defensive bases are a concern but not a ...
- 'Lost' spy satellite orbited Earth undetected for 25 years—until now, scientists sayon May 8, 2024 at 1:50 pm
An experimental spy satellite that was deemed "lost" after eluding detection for decades has finally been found. "The S73-7 satellite has been rediscovered after being untracked for 25 years," ...
- Enhancing Surveillance Privacy with Computer Visionon May 7, 2024 at 4:50 pm
Can privacy concerns be addressed as video surveillance technology continues to advance? This is what a recent award from the U.S. National Science Foundat | Technology ...
- Surveillance footage of gas purchase leads to arson, double homicide arreston May 7, 2024 at 10:19 am
Investigators pointed out that video surveillance captured at a nearby business showed a person throwing an incinerator device from an SUV towards the business before the fire. A homicide ...
- Surveillance Equipment Discovered in Room Intended for Polish Government Meetingon May 7, 2024 at 3:52 am
Bugging devices were detected in a room in Katowice where Polish Prime Minister Donald Tusk was scheduled to meet with his Cabinet. The devices, which could be used for recording or eavesdropping, ...
- Chinese-Made Surveillance Cameras Are Spreading Across Eastern Europe, Despite Security Concernson May 6, 2024 at 12:00 am
Despite growing concerns over lax data practices, security vulnerabilities, and ties to the Chinese state, the world’s two largest manufacturers of surveillance cameras are expanding across Central ...
- Threats of Surveillance Equipmenton May 5, 2024 at 12:15 pm
The surreptitious purchase of surveillance devices is a threat to democracy and to people’s rights to privacy. It is also prone to embezzlement and abuse.
- Security News This Week: A New Surveillance Tool Invades Border Townson May 4, 2024 at 3:30 am
Plus: An assassination plot, an AI security bill, a Project Nimbus revelation, and more of the week’s top security news.
- How to Spy on Devices Connected to Your Wi-Fion May 3, 2024 at 1:30 am
In this guide, we’ll teach you how to spy on devices connected to Wi-Fi. This lets you monitor anyone’s device and track their activities while connected to your Wi-Fi. For instance ...
The Latest Google Headlines on:
Surveillance devices
[google_news title=”” keyword=”surveillance devices” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]