Researchers have developed a new method to overcome one of the main issues in implementing a quantum cryptography system, raising the prospect of a useable ‘unbreakable’ method for sending sensitive information hidden inside particles of light.
By ‘seeding’ one laser beam inside another, the researchers, from the University of Cambridge and Toshiba Research Europe, have demonstrated that it is possible to distribute encryption keys at rates between two and six orders of magnitude higher than earlier attempts at a real-world quantum cryptography system. The results are reported in the journal Nature Photonics.
Encryption is a vital part of modern life, enabling sensitive information to be shared securely. In conventional cryptography, the sender and receiver of a particular piece of information decide the encryption code, or key, up front, so that only those with the key can decrypt the information. But as computers get faster and more powerful, encryption codes get easier to break.
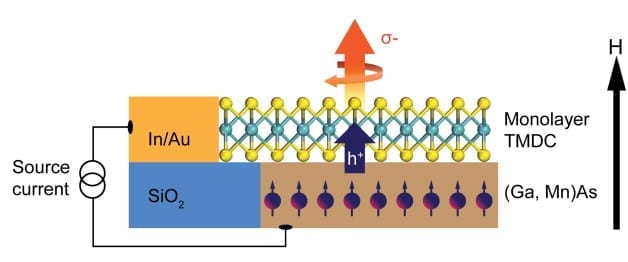
Quantum cryptography promises ‘unbreakable’ security by hiding information in particles of light, or photons, emitted from lasers. In this form of cryptography, quantum mechanics are used to randomly generate a key. The sender, who is normally designated as Alice, sends the key via polarised photons, which are sent in different directions. The receiver, normally designated as Bob, uses photon detectors to measure which direction the photons are polarised, and the detectors translate the photons into bits, which, assuming Bob has used the correct photon detectors in the correct order, will give him the key.
The strength of quantum cryptography is that if an attacker tries to intercept Alice and Bob’s message, the key itself changes, due to the properties of quantum mechanics. Since it was first proposed in the 1980s, quantum cryptography has promised the possibility of unbreakable security. “In theory, the attacker could have all of the power possible under the laws of physics, but they still wouldn’t be able to crack the code,” said the paper’s first author Lucian Comandar, a PhD student at Cambridge’s Department of Engineering and Toshiba’s Cambridge Research Laboratory.
However, issues with quantum cryptography arise when trying to construct a useable system. In reality, it is a back and forth game: inventive attacks targeting different components of the system are constantly being developed, and countermeasures to foil attacks are constantly being developed in response.
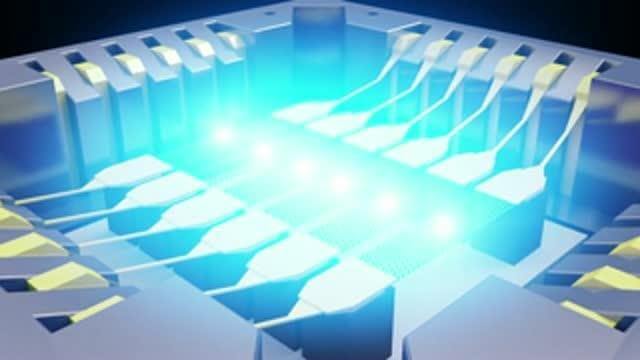
The components that are most frequently attacked by hackers are the photon detectors, due to their high sensitivity and complex design – it is usually the most complex components that are the most vulnerable. As a response to attacks on the detectors, researchers developed a new quantum cryptography protocol known as measurement-device-independent quantum key distribution (MDI-QKD).
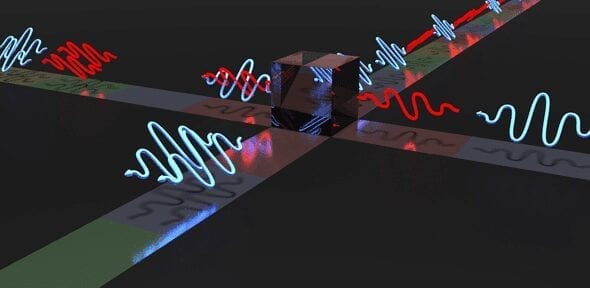
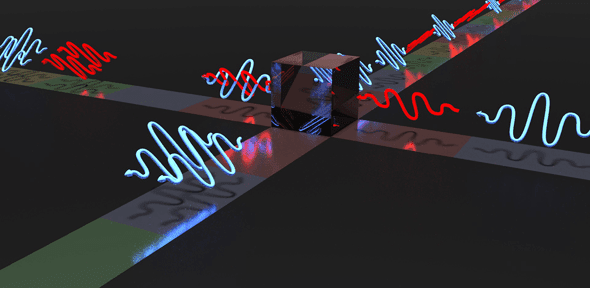
In this method, instead of each having a detector, Alice and Bob send their photons to a central node, referred to as Charlie. Charlie lets the photons pass through a beam splitter and measures them. The results can disclose the correlation between the bits, but not disclose their values, which remain secret. In this set-up, even if Charlie tries to cheat, the information will remain secure.
MDI-QKD has been experimentally demonstrated, but the rates at which information can be sent are too slow for real-world application, mostly due to the difficulty in creating indistinguishable particles from different lasers. To make it work, the laser pulses sent through Charlie’s beam splitter need to be (relatively) long, restricting rates to a few hundred bits per second (bps) or less.
The method developed by the Cambridge researchers overcomes the problem by using a technique known as pulsed laser seeding, in which one laser beam injects photons into another. This makes the laser pulses more visible to Charlie by reducing the amount of ‘time jitter’ in the pulses, so that much shorter pulses can be used. Pulsed laser seeding is also able to randomly change the phase of the laser beam at very high rates.
The result of using this technique in a MDI-QKD setup would enable rates as high as 1 megabit per second, representing an improvement of two to six orders of magnitude over previous efforts.
“This protocol gives us the highest possible degree of security at very high clock rates,” said Comandar. “It could point the way to a practical implementation of quantum cryptography.”
Learn more: Laser technique promises super-fast and super-secure quantum cryptography
The Latest on: Quantum cryptography
[google_news title=”” keyword=”quantum cryptography” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]
via Google News
The Latest on: Quantum cryptography
- Swiss startup unveils post-quantum cryptography library for devson May 8, 2024 at 5:00 am
Swiss startup Terra Quantum has released an open-source repository for quantum-resistant encryption algorithms.
- nodeQ Launches PQtunnel: The Leading-Edge Cybersecurity Solution for Quantum-Safe Communicationon May 7, 2024 at 2:52 pm
The latest application developed by nodeQ simplifies the migration to Post-Quantum Cryptography for both SMEs and large enterprises YORK, England, May 7, 2024 /PRNewswire/ -- The advent ...
- DigiCert addresses quantum threats and AI challenges in digital securityon May 7, 2024 at 11:46 am
DigiCert, a digital certificate provider, aims to secure the digital landscape. Explore its solutions for identity, access and quantum readiness.
- nodeQ Launches PQtunnelTM: The Leading-Edge Cybersecurity Solution for Quantum-Safe Communicationon May 7, 2024 at 10:26 am
The advent of Quantum Computing poses a significant threat to existing public-key cryptosystems. A large quantum computer can break algorithms like RSA or ECDH, which form the backbone of current ...
- Future Proof Encryption: Embracing Post-Quantum Cryptography For Quantum-Resilient Solutionson May 7, 2024 at 5:45 am
Let's look at how computing technology could challenge today's encryption protocols and the potential ways to secure ourselves.
- QANplatform launches world’s first quantum-resistant, EVM-compatible testneton May 6, 2024 at 4:59 pm
Apple unveiled a new update in February that aims to future-proof iMessages with post-quantum cryptography, making Apple the first among a handful of quantum-proof messaging providers. The Signal ...
- Keysight introduces new testing capabilities to strengthen post-quantum cryptographyon May 6, 2024 at 5:36 am
Keysight Technologies, Inc. has announced industry-first testing capabilities designed to test the robustness of post-quantum cryptography (PQC). This latest addition to Keysight Inspector is a ...
- Quantum Cryptography Market Innovative Strategies for Harnessing Future Market Size Growthon May 2, 2024 at 2:11 am
The “Global Quantum Cryptography Market 2024“ research describes the competitive market environment based on production volume, profits, and sales. The report covers even the supply chain analysis of ...
- Google Chrome's new post-quantum cryptography is causing some issueson April 29, 2024 at 3:00 am
Some sites are refusing to work with Chrome 124’s default quantum-resistant hybridized tool – here’s what to do.
- Google Chrome's new post-quantum cryptography may break TLS connectionson April 28, 2024 at 7:19 am
Some Google Chrome users report having issues connecting to websites, servers, and firewalls after Chrome 124 was released last week with the new quantum-resistant X25519Kyber768 encapsulation ...
via Bing News