Researchers from North Carolina State University have developed a software algorithm that detects and isolates cyber-attacks on networked control systems – which are used to coordinate transportation, power and other infrastructure across the United States.
Networked control systems are essentially pathways that connect and coordinate activities between computers and physical devices. For example, the systems that connect temperature sensors, heating systems and user controls in modern buildings are networked control systems.
But, on a much larger scale, these systems are also becoming increasingly important to national infrastructure, such as transportation and power. And, because they often rely on wireless or Internet connections, these systems are vulnerable to cyber-attacks. “Flame” and “Stuxnet” are examples of costly, high-profile attacks on networked control systems in recent years.
As networked control systems have grown increasingly large and complex, system designers have moved away from having system devices – or “agents” – coordinate their activities through a single, centralized computer hub, or brain. Instead, designers have created “distributed network control systems” (D-NCSs) that allow all of the system agents to work together, like a bunch of mini-brains, to coordinate their activities. This allows the systems to operate more efficiently. And now these distributed systems can also operate more securely.
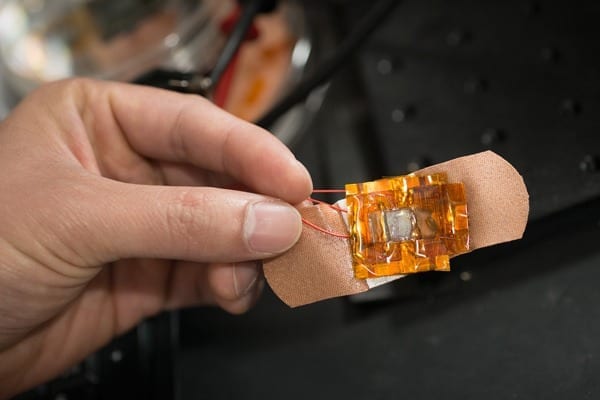
NC State researchers have developed a software algorithm that can detect when an individual agent in a D-NCS has been compromised by a cyber-attack. The algorithm then isolates the compromised agent, protecting the rest of the system and allowing it to continue functioning normally. This gives D-NCSs resilience and security advantages over systems that rely on a central computer hub, because the centralized design means the entire system would be compromised if the central computer is hacked.
The Latest Bing News on:
Cyber attacks
- Bipartisan Push for Water Security, Reps Gallego and Fallon Urge Federal Action on Cyber Threats After Texas Attackon April 27, 2024 at 1:40 am
Reps. Gallego and Fallon urge Homeland Security to detail defenses after a Russian-linked group targets Texas water system.
- Tong Joins AGs Pressing United Health Group To Better Respond To The Feb. 1 Cyber Attack On Change Healthcareon April 26, 2024 at 4:29 pm
Connecticut Attorney General William Tong has joined a multi-state coalition of 22 attorneys general urging United Health Care Inc. to take more proactive action to protect healthcare providers, ...
- Utilities are facing unprecedented cyber threats. What should they do about it?on April 26, 2024 at 2:37 pm
Earlier this year, the FBI issued a stark warning: critical infrastructure assets in the U.S. were the target of Chinese government hackers.
- Inside Rising Cyber Attacks: Tackling Insurance Hikes, Payment Disruptions at Nursing Homeson April 26, 2024 at 1:50 pm
Health care cyber attacks have been an ever-present threat for providers, including nursing homes. But the most recent attacks on Change Healthcare have ...
- Cyber attack forces KC Scout’s website, traffic cameras, message boards to shut downon April 25, 2024 at 1:12 pm
During the shutdown, people needing traffic information should visit MoDOT KC’s social media sites on X and Facebook or call 888-275-6636. For Kansas Department of Transportation traffic information, ...
- How a crippling cyber attack on a U.S. healthcare company is impacting Pueblo physicianson April 25, 2024 at 12:00 pm
Family practice physician Dr. Rakesh Khosla is among the rural health providers whose financial systems have been paralyzed by a recent cyber attack.
- Frontier Communications Cyber Attack Shuts Down Systems, Leaks Personal Dataon April 25, 2024 at 9:00 am
A cyber attack by a suspected cybercrime group has forced Frontier Communications, a Dallas, Texas-based optic-fiber Internet provider, to temporarily shut down its information systems to contain the ...
- The cyber landscape in 2024: AI, cyber attacks and disinformationon April 25, 2024 at 7:07 am
Cyber attacks and disinformation to both rise. The potential extent, scale, and speed with which technology can be used to disrupt organisations and information flows is unprecede ...
- US Sanctions Iranian "Fronts" for Cyber-Attacks on American Entitieson April 24, 2024 at 6:45 am
The US Treasury announced sanctions on two companies and four individuals for cyber campaigns conducted on behalf of the Iranian government ...
- Are We Ready for a Cyber Attack on Food and Farming?on April 23, 2024 at 2:07 pm
Authorities are working to prepare for one by, for the first time, conducting a massive federal tabletop exercise focused on food and agriculture cybersecurity resilience.
The Latest Google Headlines on:
Cyber attacks
[google_news title=”” keyword=”cyber attacks” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]
The Latest Bing News on:
Distributed network control systems
- Satoshi created a way, gave it away, and walked away – Michael Sayloron April 27, 2024 at 9:12 am
Michael Saylor, the vocal Bitcoin supporter and founder of MicroStrategy, sparked a discussion about Satoshi Nakamoto, the enigmatic creator of Bitcoin - in a recent X activity.
- The Future of Money: How Cryptocurrency is Transforming the Financial Industryon April 26, 2024 at 11:27 am
Welcome to the future of money, where digital currencies are revolutionizing the financial industry as we know it. With cryptocurrency gaining traction around the world, traditional forms of currency ...
- Bitcoin Is Built To Last: How The Network Defends Against Attackson April 26, 2024 at 9:30 am
Bitcoin is not invincible, but was designed with resilience at its core. The eighth installment of “10 Steps to Self-Sovereignty” powered by Ledger.
- Exploring the Impact of Blockchain in Advertisingon April 26, 2024 at 9:23 am
From combating ad fraud to revolutionizing data privacy, the applications of blockchain in advertising are vast and transformative. Let’s delve deeper into how this innovative technology is reshaping ...
- Command and Control (C2) System market is projected to grow at a CAGR of 6.4% by 2034: Visiongainon April 26, 2024 at 7:25 am
Visiongain has published a new report entitled Command and Control (C2) System Market Report 2024-2034: Forecasts by Component (Hardware, Software), by Software (Command and Control Software, ...
- Distributed cloud may solve data management challengeson April 26, 2024 at 7:13 am
At the forefront of cybersecurity concerns is data sovereignty. Despite major cloud providers’ best efforts to align with strict regulations such as NIS2, ISO 27001, and GDPR, the landscape remains ...
- Optimizing IoT Networks In An Increasingly Smart, Interconnected Worldon April 24, 2024 at 5:29 am
Customers expect IoT functionality to be always on and responsive, and outages and delays can hurt your brand reputation and your bottom line.
- Distributed Energy Resource Management System Market Size to Surpass USD 1.97 Billion by 2031 with a CAGR of 19.4% from 2024 to 2031on April 22, 2024 at 9:38 am
Distributed Energy Resource Management System Market Size to Surpass USD 197 Billion by 2031 with a CAGR of 194 from 2024 to 2031 ...
- Securing the edge: A new battleground in mobile network securityon April 22, 2024 at 5:03 am
Edge computing is now a reality that’s reshaping industries and transforming approaches to mobile network infrastructure, but failure to secure it can expose networks and data to cyber threats. Learn ...
- Distributed Control Systems (DCS) Market Outlook, Share, Top Players, Revenue, Size and Forecast to 2024 to 2032on April 14, 2024 at 10:10 pm
The emerging process industries are merely operated by advanced automation technologies such as distributed control systems (DCS). These systems are used as an extension of traditional controllers ...
The Latest Google Headlines on:
Distributed network control systems
[google_news title=”” keyword=”distributed network control systems” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]