via knowcache.com
New hacking technique imperceptibly changes memory virtual servers
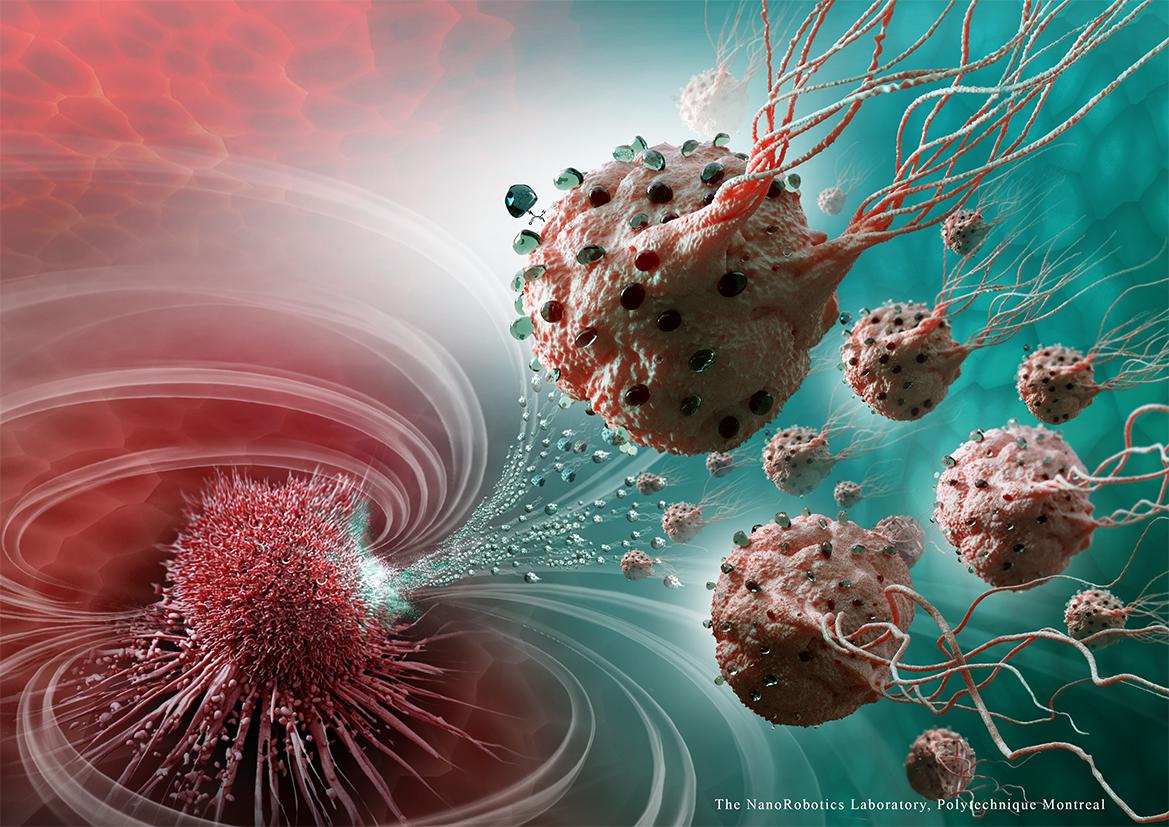
For the first time ever a team of Dutch hacking experts, led by cyber security professor Herbert Bos, managed to alter the memory of virtual machines in the cloud without a software bug, using a new attack technique.
With this technique an attacker can crack the keys of secured virtual machines or install malware without it being noticed. It’s a new deduplication-based attack in which data can not only be viewed and leaked, but also modified using a hardware glitch. By doing so the attacker can order the server to install malicious and unwanted software or allow logins by unauthorized persons.
Deduplicationand Rowhammer bug
With the new attack technique Flip Feng Shui (FSS), an attacker rents a virtual machine on the same host as the victim. This can be done by renting many virtual machines until one of them lands next to the victim. A virtual machine in the cloud is often used to run applications, test new software, or run a website. There are public (for everyone), community (for a select group) and private (for one organization accessible) clouds. The attacker writes a memory page that he knows exists in the victim on the vulnerable memory location and lets it deduplicate. As a result, the identical pages will be merged into one in order to save space (the information is, after all, the same). That page is stored in the same part of the memory of the physical computer. The attacker can now modify the information in the general memory of the computer. This can be done by triggering a hardware bug dubbed Rowhammer, which causes flip bits from 0 to 1 or vice versa, to seek out the vulnerable memory cells and change them.
Cracking OpenSSH
The researchers of the Vrije Universiteit Amsterdam, who worked together with a researcher from the Catholic University of Leuven, describe in their research two attacks on the operating systems Debian and Ubuntu. The first FFS attack gained access to the virtual machines through weakening OpenSSH public keys. The attacker did this by changing the victim’s public key with one bit. In the second attack, the settings of the software management application apt were adjusted by making minor changes to the URL from where apt downloads software. The server could then install malware that presents itself as a software update. The integrity check could be circumvented by making a small change to the public key that verifies the integrity of the apt-get software packages.
Advise NSCS
Debian, Ubuntu, OpenSSH and other companies included in the research were notified before the publication and all have responded. The National Cyber Security Centre (NSCS) of the Dutch government has issued a fact sheet containing information and advice on FFS.
‘Hack-Oscar’
The researchers presented their findings this week during the UNESIX Security Symposium 2016 in the United States. Recently they won the Oscar of hacking: the Pwnie for another attack technique that allows attackers to take over state-of-the-art software (such as the new Edge browser on Microsoft Windows) with all defences up, even if the software has no bugs. Moreover, they can do this from JavaScript in the browser.
Learn more: New hacking technique imperceptibly changes memory virtual servers
The Latest on: Hacking
[google_news title=”” keyword=”hacking” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]
via Google News
The Latest on: Hacking
- Armed with machetes, three men go on hacking spree in Chennai, attack 12on April 26, 2024 at 10:41 pm
Three men armed with machetes attacked 12 people in Thirumullaivoyal. Two arrested, one absconding. They were air-conditioner mechanics. The gang targ ...
- Stellar Blade: How To Unlock Drone Hacking Toolon April 26, 2024 at 10:09 pm
Players will need the Drone Hacking Tool to unlock High-Security Sealed Chests in Stellar Blade. Here's how to get it.
- Hacking the Narrative: Cyber Manhunt 2: New World Arrives on Steam Early Accesson April 26, 2024 at 3:30 pm
New World Sets to Hack Its Way into Gamers Hearts via Steam Early Access on May 10 Gear up, digital sleuths! Spiral Up Games just dropped the byte-sized bomb that their latest narrative-driven ...
- How to get the Hacking Tool in Stellar Bladeon April 25, 2024 at 5:01 am
Takes you closer to the games, movies and TV you love ...
- Hacking and Healing: Nation-States, Cyber Attacks, and Healthcare Lawon April 24, 2024 at 5:00 pm
In recent years, one of the most alarming aspects of cyber warfare is the targeted hacking of healthcare platforms, electronic medical records, and genomic databases. Healthcare systems are ...
- Prompt Hacking, Private GPTs, Zero-Day Exploits and Deepfakes: Report Reveals the Impact of AI on Cyber Security Landscapeon April 24, 2024 at 4:12 pm
A new report by cyber security firm Radware identifies the four main impacts of AI on the threat landscape emerging in 2024.
- Four Iranian men accused of yearslong hacking campaign against Treasury and State departments remain at largeon April 23, 2024 at 7:22 pm
Four Iranian men were charged by prosecutors on Tuesday for allegedly orchestrating a hacking campaign that targeted U.S. federal agencies and more than 12 defense contractors handling classified ...
- North Korea hacking teams hack South Korea defence contractors - policeon April 22, 2024 at 11:18 pm
Major North Korean hacking groups have mounted "all-out" cyber attacks against South Korean defence companies for more than a year, breaching the firms' internal networks and stealing technical data, ...
- Alabama high school prepares students with STEM, cyber and hacking classeson April 22, 2024 at 6:58 pm
The Alabama School of Cyber Technology and Engineering is a hybrid boarding school working to prepare students for the AI-infused workplace.
- Russia-linked hacking group claims to have targeted Indiana water planton April 22, 2024 at 1:08 pm
Hackers targeted a wastewater treatment plant in Indiana on Friday evening, prompting plant managers to send maintenance personnel to investigate the suspicious activity, a local official told CNN.
via Bing News