via LMU
Researchers at LMU and the University of Singapore have experimentally realized an expanded form of quantum cryptography for the first time.
- Its coding protocol is device-independent, making it even more secure than previous quantum cryptographic methods.
- The research lays the foundation for future quantum networks, in which absolutely secure communication is possible between far distant locations.
The Internet is teeming with highly sensitive information. Sophisticated encryption techniques generally ensure that such content cannot be intercepted and read. But in the future high-performance quantum computers could crack these keys in a matter of seconds.
Quantum key distribution (QKD) – as the jargon has it – is secure against attacks on the communication channel. This renders QKD immune against outside attacks from quantum computers, but not against attacks from or manipulations of the devices themselves. The devices could output a key which the manufacturer had previously saved and might conceivably have forwarded to a hacker. But device-independent QKD (abbreviated to DIQKD) is capable of testing the security of the devices. Theoretically known since the 1990s, this method has now been experimentally realized for the first time, by an international research group led by LMU physicist Harald Weinfurter and Charles Lim from the National University of Singapore (NUS).
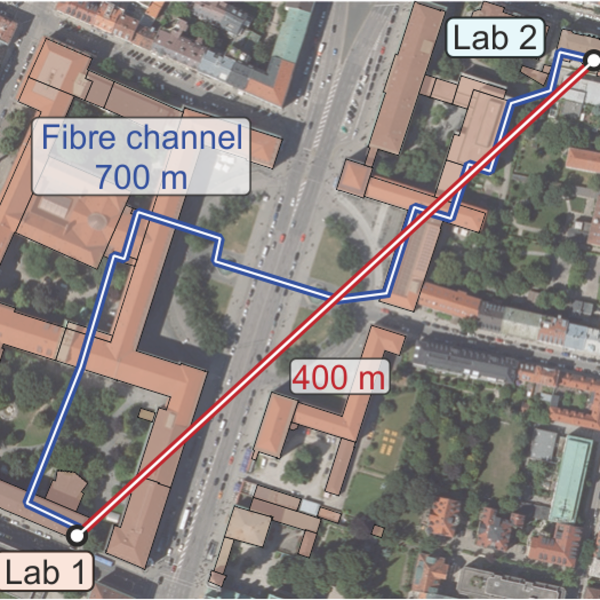
In the present experiment, the physicists used two entangled rubidium atoms, situated in two laboratories located 400 meters from each other on the LMU campus, for the key distribution. The two locations are connected via a fiber optic cable 700 meters in length, which runs beneath Geschwister Scholl Square in front of the main building.
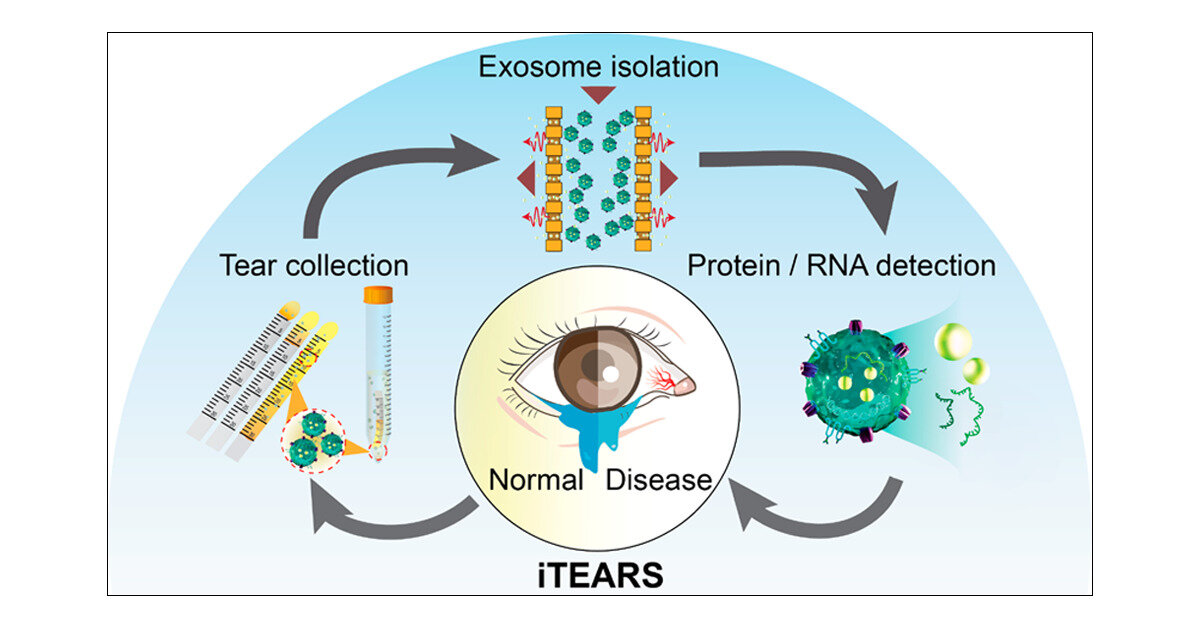
To exchange a key, the two parties measure the quantum states of their atoms. In each case, this is done randomly in two or four directions. If the directions correspond, the measurement results are identical on account of entanglement and can be used to generate a secret key. With the other measurement results, a so-called Bell inequality can be evaluated. John Bell originally developed these inequalities to test whether nature can be described with hidden variables. In DIQKD, the test is now being used “to ensure that there are no manipulations at the devices – that is to say, that hidden measurement results have not been saved in the devices beforehand,” explains Weinfurter.
The NUS protocol now uses two measurement settings. “This makes it much more difficult to intercept information. And so more noise can be tolerated and secret keys can be generated even when there is more noise,” says Charles Lim.
“With our method, we can securely generate secret keys even with uncharacterized and potentially untrustworthy devices,” explains Weinfurter. “Our work lays the foundation for future quantum networks, in which absolutely secure communication is possible between far distant locations,” says Charles Lim.
Original Article: Quantum cryptography: Hacking futile
More from: Ludwig Maximilian University of Munich | National University of Singapore
The Latest Updates from Bing News & Google News
Go deeper with Bing News on:
Quantum cryptography
- WISeKey Semiconductors S.A.S Rebranded as SEALSQ France S.A.S to Expand Post-Quantum Semiconductor Development in Meyreuil, Aix-en-Provence
NDAQ:LAES) WISeKey Semiconductors S.A.S Rebranded as SEALSQ France S.A.S to Expand Post-Quantum Semiconductor Development in Meyreuil, Aix-en-Provence ...
- Keysight introduces post-quantum cryptography testing capabilities
Keysight Technologies has announced an automated solution designed to test the robustness of post-quantum cryptography (PQC).
- Defence policy update focuses on quantum technology’s role in making Canada safe
A major focus of the federal government’s defence policy update is the need to develop quantum-based defence technology that will help Canada address two big threats: the Arctic and cyber security.
- Keysight Introduces New Testing Capabilities to Strengthen Post-Quantum Cryptography
Keysight Technologies, Inc. (NYSE: KEYS), has announced an industry-first automated solution designed to test the robustness of post-quantum cryptography (PQC). This latest addition to Keysight ...
- Arqit announces collaboration to deliver out-of-the-box post-quantum cryptography solutions
LONDON, April 29, 2024 (GLOBE NEWSWIRE) -- Arqit Quantum Inc. (Nasdaq: ARQQ, ARQQW) (Arqit), a leader in quantum-safe encryption, today announced the creation of the World’s First Quantum-Safe, 1.89 ...
Go deeper with Google Headlines on:
Quantum cryptography
[google_news title=”” keyword=”quantum cryptography” num_posts=”5″ blurb_length=”0″ show_thumb=”left”]
Go deeper with Bing News on:
Quantum networks
- Novo plans $200m investment in quantum computing startups
The Novo Holdings funds will focus on investment in companies developing quantum computing, sensing, and algorithms with applications in healthcare.
- Intel Takes Next Step Toward Building Scalable Silicon-Based Quantum Processors
(Credit: Intel Corporation) Quantum hardware researchers from Intel developed a ... By embedding intelligence in the cloud, network, edge and every kind of computing device, we unleash the potential ...
- Lead-vacancy centers in diamond as building blocks for large-scale quantum networks
A lead-vacancy (PbV) center in diamond has been developed as a quantum emitter for large-scale quantum networks by researchers. This innovative color center exhibits a sharp zero-phonon-line and emits ...
- PSiQuantum to build first utility-scale quantum computer in Australia
The Australian government has invested US$620 million in startup PSiQuantum to build a fault-tolerant quantum system for commercial use.
- Australia just made a billion-dollar bet on building the world's first 'useful' quantum computer
The Australian government has announced a pledge of approximately A$940 million (US$617 million) to PsiQuantum, a quantum computing start-up company based in Silicon Valley.
Go deeper with Google Headlines on:
Quantum networks
[google_news title=”” keyword=”quantum networks” num_posts=”5″ blurb_length=”0″ show_thumb=”left”]