via Fraunhofer SIT
In the wake of the revelations that intelligence agencies have been engaged in mass surveillance activities, both industry and society at large are looking for practicable encryption solutions that protect businesses and individuals.
Previous technologies have failed in practice because they were too expensive or not user friendly enough. Fraunhofer has launched an open initiative called “Volksverschlüsselung” with the aim of bringing end-to-end encryption to the masses. Fraunhofer researchers will be presenting a prototype of their easy-to-use software and the infrastructure concept behind it at CeBIT 2015 (Hall 9, Booth E40).
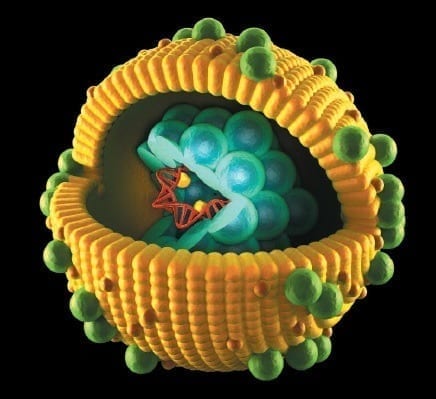
Encryption is the most effective antidote to unwarranted, mass surveillance of people, companies and authorities. Although there are any number of computer programs designed to, say, make e-mail communication more secure, most people find them to be too much of a hassle. This is why the German government made establishing universal and easy-to-use encryption part of its Digital Agenda. A research team from the Fraunhofer Institute for Secure Information Technology SIT in Darmstadt developed a public encryption concept that factors in user friendliness from the outset. The software automatically installs the cryptographic keys in the right places on your computer. The researchers are also working on an infrastructure that will be available to everyone and is compatible with existing encryption services.
“With this initiative and what it’s developing, Fraunhofer is supporting the German government’s efforts to better protect people and companies,” says Prof. Michael Waidner, Head of Fraunhofer SIT. This is why “Volksverschlüsselung“ is to be made available as open-source software.
Key allocation for beginners
The software is the centerpiece of the solution. It relieves the user of the previously difficult task of allocating keys by recognizing which applications – different e-mail programs, for example – on your computer, smartphone or tablet can use cryptography and automatically allocates the right key to each one. The software also generates cryptographic keys that can be used to encrypt e-mails or files.
If you want to send someone an encrypted e-mail, you need the public key. In the “Volksverschlüsselung“ model, you can obtain this from the central infrastructure. “It works like a phone book,” says project manager Michael Herfert. “Anyone can look up and download public keys. The central infrastructure also ensures that the keys actually belong to the person requesting them and helps prevent identity fraud.”
Read more: Encryption for everyone
The Latest on: Encryption
[google_news title=”” keyword=”Encryption” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]
via Google News
The Latest on: Encryption
- New Spectre-Style 'Pathfinder' Attack Targets Intel CPU, Leak Encryption Keys and Dataon May 8, 2024 at 7:17 am
Researchers have uncovered a new class of attacks called Pathfinder that can extract encryption keys and sensitive data from Intel CPUs.
- Windows 11 to receive default BitLocker encryption, new RAM speed metrics in Task Manageron May 8, 2024 at 6:43 am
Update is on its way, and it will seemingly try to enable BitLocker disk encryption by default during installation. According to ...
- European Threat To End-To-End Encryption Would Invade Phoneson May 7, 2024 at 10:52 am
European policymakers are discussing a law that might put a screening algorithm on millions of user devices - posing a dire threat to digital privacy.
- Europol’s declaration against end-to-end encryption reignites debate, sparks privacy concernson May 7, 2024 at 5:50 am
[Euractiv illustration by Esther Snippe, photos by Shutterstock] Europol’s recent joint declaration with European police chiefs urges action against end-to-end encryption, citing concerns of possible ...
- Future Proof Encryption: Embracing Post-Quantum Cryptography For Quantum-Resilient Solutionson May 7, 2024 at 5:45 am
Let's look at how computing technology could challenge today's encryption protocols and the potential ways to secure ourselves.
- End-to-end encryption may be the bane of cops, but they can't close that Pandora's Boxon May 5, 2024 at 6:30 am
Internet Society's Robin Wilton tells us the war on privacy won't be won by the plod interview Police can complain all they like about strong end-to-end encryption making their jobs harder, but it ...
- Microsoft plans to lock down Windows DNS like never before. Here’s how.on May 3, 2024 at 4:42 pm
Microsoft on Friday provided a peek at a comprehensive framework that aims to sort out the Domain Name System (DNS) mess so that it’s better locked down inside Windows networks. It’s called ZTDNS ...
- It Turns Out Marriott Wasn't Using Encryption Before Huge Data Breachon May 1, 2024 at 3:30 pm
Marriott experienced a massive breach that exposed details of 500 million guests over a four-year period. At the time, Marriott claimed that its data was secured by AES-128 encryption but now admits ...
- Encyro: Email Encryption Your Clients Will Loveon May 1, 2024 at 4:59 am
Secure all outgoing and incoming email communication by using an email encryption service. Encyro makes it easy to send and receive encrypted emails for free.
- Marriott admits it falsely claimed for five years it was using encryption during 2018 breachon April 29, 2024 at 4:04 pm
Marriot revealed in a court case around a massive 2018 data breach that it had been using secure hash algorithm 1 and not the much more secure AES-1 encryption as it had earlier maintained.
via Bing News