The danger from an audio botnet would be considerable
The computer scientists Michael Hanspach and Michael Goetz of the Fraunhofer Institute for Communication, Information Processing and Ergonomics FKIE have proven that computers can create hidden networks via inaudible sound. Michael Hanspach confirmed media coverage on the topic in a radio interview with Hessischer Rundfunk yesterday. Hanspach and his colleague had successfully transmitted data from one computer to another without providing a connection via wireless LAN, network cards or the internet. This was made possible through audio signals emitted from a loudspeaker and received by a microphone.
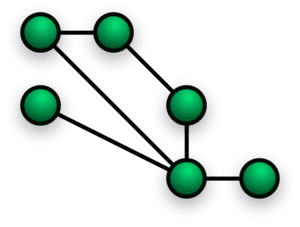
In an experiment that was published in the Journal of Communications in November Michael Hanspach and Michael Goetz studied how computers can connect to each other in an inaudible acoustic network and exchange data. In the mesh network the computers were not connected to a central access point or router which would be the case in a conventional wireless LAN network. The scientists chose a near ultrasonic frequency range. The results of the experiment: The computers communicated with each other within a range of up to 20 m (19.7 meters, 64.6 feet) using their built-in loudspeakers and microphones.
That wasn’t all: In the experiment which involved five computers the signals could be transmitted from one computer to another until one computer with a regular internet connection took the signal “outside”. This result might also be achieved with smartphones or tablets, says Michael Hanspach. Would it be possible to infect computers with malware this way? Hanspach is sceptical that the malware “badBIOS” exists in the manner that was discussed in the technology news articles of the past weeks. However, what sounds like science fiction today might well be reality in five years, the scientist says. The danger from an audio botnet would be considerable. This applies to critical infrastructures, for example.
The Latest on: Audio botnet
- The Surveillance Invasion: IoT and Smart Devices Stealing Corporate Secretson May 2, 2024 at 3:00 am
Chris Clements, VP of Solutions Architecture at CISO Global “Hey Alexa, are you stealing my company’s data?” In an age where manufacturers have decided that just about every device needs to be “smart, ...
- Smashing Security podcast #370: The closed loop conundrum, default passwords, and Baby Reindeeron May 1, 2024 at 4:40 pm
The UK Government takes aim at IoT devices shipping with weak or default passwords, an identity thief spends two years in jail after being mistaken for the person who stole his name, and are you au ...
- Rogue Algorithms: How AI Is Being Used For Terrorismon April 29, 2024 at 6:13 pm
As dependency on AI has increase (especially after the COVID 19 pandemic) it has portrayed many malicious behaviours showcasing the capacity of AI’s for potential cyberattacks, leading to thefts of ...
- How a Massive Hack of Psychotherapy Records Revealed a Nation’s Secretson April 22, 2024 at 1:00 am
Aleksanteri Kivimäki was a hacker wunderkind with a mean streak. Now he’s on trial for the largest crime in Finland’s history.
- Russian US election interference sowing discord over Ukraine kicks into gearon April 17, 2024 at 2:55 pm
Microsoft also noted that the governments of China and Iran are also actively aiming to influence the outcome of the November elections, although not to the extent the Russian government is. “Like ...
- How tech giants cut corners to harvest data for AIon April 15, 2024 at 6:00 am
OpenAI, Google and Meta ignored corporate policies, altered their own rules and discussed skirting copyright law as they sought information to train their newest AI systems.
via Bing News
The Latest on: Inaudible acoustic network
- Feed has no items.
via Bing News