When Web surfers sign up for a new online service or download a Web application for their smartphone or tablet, the service typically requires them to click a seemingly innocuous box and accept the company’s terms of service and privacy policy.
But agreeing to terms without reading them beforehand can adversely affect a user’s legal rights, says a new paper by a University of Illinois expert in technology and legal issues.
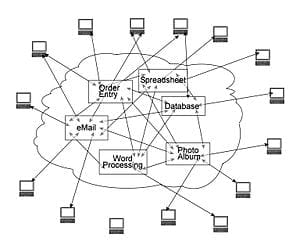
Law professor Jay P. Kesan says the current “non-negotiable approach” to user privacy is in need of serious revision, especially with the increased popularity of Web-based software that shares information through cloud computing.
In a recently published paper in the Washington and Lee Law Review, Kesan and co-authors Carol M. Hayes, a research associate in the College of Law, and Masooda N. Bashir, the assistant director of the Social Trust Initiatives at the U. of I.’s Information Trust Institute, propose creating a legal framework that would require companies to provide baseline protections for personal information while also taking steps to enhance users’ control over their own data.
“Our goal with this piece is to raise awareness of the privacy of online information, which is something that people seem to care about a lot more once they actually know what companies are doing with their personal information and data,” said Kesan, the H. Ross & Helen Workman Research Scholar in the College of Law.
With so many of our daily activities now taking place “in the cloud,” Kesan cautions it’s still perfectly acceptable for users to give away personal information to online services – so long as they’re comfortable with allowing companies to snoop, aggregate and data mine their online habits.
“If you think it’s a fair trade to receive an email service in exchange for letting a company track what Web pages you visit and show you relevant advertisements, by all means, you should continue to do so,” Kesan said. “But there are always security risks involved when information is stored, electronically or not. Users must weigh the advantages and disadvantages of the available options.”
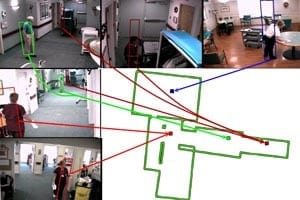
In the article, the scholars analyzed and categorized terms-of-service agreements and privacy policies of several major cloud-based services to assess the state of user privacy. Their analysis shows that providers all take similar approaches to user privacy, in that providers were consistently more detailed when describing the user’s obligations to the provider than when describing the provider’s obligations to the user.
“It’s the provider who sets the terms, knows the terms inside and out, and ultimately benefits from the terms,” Kesan said. “But because these obligations are usually in the form of an ‘adhesion contract,’ and only one party has bargaining power, the consumer does not have the ability to counter with new terms, ones that could increase their benefits.”
In the article, the authors describe personal information as being akin to online currency.
“You’re essentially bartering with a lot of these online service providers,” Kesan said. “You give them access to your information, and they aggregate this information to create a profile of you as a consumer. Most of these companies do not outright sell your information unless you tell them that it’s OK to do so. But by giving them your information in exchange for the service, you have essentially engaged in bartering. And what we want is for people to recognize that this is a business exchange.”
And while the user gives the service what they want, the service also imposes additional terms that the user probably doesn’t read.
“So not only are these one-sided agreements that are designed to benefit the provider of the service, the consumer who clicks ‘I agree’ also is woefully under-informed about what it is that they just agreed to,” Kesan said.
“It’s very difficult to weigh the advantages and disadvantages and then make an informed decision, if you don’t know what’s actually going on. All of this additional information means that their advertising space is more valuable. But when consumers are not informed, they’re bartering their goods in exchange for one identified item and one box with unknown contents.”
That asymmetry, combined with these terms’ non-negotiable nature, led the authors to conclude that there’s a real need for “data control” in the cloud, Kesan said.
According to the authors, they define data control as consisting of two parts: data withdrawal, which is the ability to withdraw data and require a service provider to stop using or storing the user’s information; and data mobility, which is the ability to move data to a new location without being locked into a particular provider.
The Latest Bing News on:
Cloud privacy
- Alzheimer’s doesn’t cloud Michigan woman’s love for opera singingon April 27, 2024 at 7:00 am
She performed through the 1980s at venues like the Seattle Opera, Carnegie Hall and the Metropolitan Opera House and has a lengthy list of awards and accolades over the years.
- Google CEO On Owning ‘Best’ AI, 1,000 New Cloud Products And Workspace Securityon April 26, 2024 at 9:04 am
Google CEO Sundar Pichai’s bold remarks during Google’s earnings report include touting Workspace as the leader in cybersecurity, Google Cloud and YouTube having a combined $100 billion run rate by ...
- Google Cloud Posts 28 Percent Revenue Jump In Q1 2024 Thanks To AI, Says CEOon April 26, 2024 at 5:10 am
Google Cloud, the world’s third largest cloud computing company, posted revenue that climbed an impressive 28 percent year over year. Google CEO Sundar Pichai credits the growth to the benefits that ...
- The AI camera stripping away privacy in the blink of an eyeon April 25, 2024 at 7:00 am
A new camera called NUCA uses artificial intelligence to create deepfake photos of subjects by stripping away clothing in close to real time.
- Coordinate-wise monotonic transformations enable privacy-preserving age estimation with 3D face point cloudon April 23, 2024 at 1:18 pm
In a recent publication in Science China Life Sciences, a research team led by Professor Jing-Dong Jackie Han and Ph.D. student Xinyu Yang from Peking University established a deep learning model for ...
- The cloud is not a slam dunk platform for generative AIon April 23, 2024 at 2:03 am
With public cloud providers chasing generative AI, it may be a surprise when dollars flow in other directions. Vendors and customers have a lot to consider.
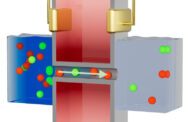
- Breakthrough in Quantum Cloud Computing Ensures its Security and Privacyon April 22, 2024 at 6:33 am
Businesses are one step closer to quantum computing thanks to a breakthrough made in its security by scientists at Oxford University.
- Q&A: Cloud migration mistakes in 2024on April 21, 2024 at 1:34 pm
Staying competitive often hinges on embracing innovative solutions. Cloud technology is a powerful tool for businesses.
- Cloud companies may lease your images for AI learning; what can you do about it?on April 21, 2024 at 6:06 am
Popular photo sharing service Photobucket recently revealed that the 13 billion images it hosts online could be used to train AI models. We explain what changes made this possible and suggest some ...
- The Widening Overlap Between Cloud Workloads and Cybersecurityon April 17, 2024 at 4:13 am
Cloud workloads can end up in a malefactor’s spotlight because they serve as conduits to accessing the wider applications they belong to.
The Latest Google Headlines on:
Cloud privacy
[google_news title=”” keyword=”cloud privacy” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]
The Latest Bing News on:
User privacy
- Apple Partners with OpenAI for On-Device AI in iOS 18, Enhancing Privacyon April 27, 2024 at 5:16 am
Apple Inc. has reignited discussions with OpenAI to integrate advanced AI features into iOS 18, utilizing large language models entirely on-device. According to a Bloomberg report, this move promises ...
- Ring Settlement FAQ: Here's Why Home Security Users Like You Are Getting Paidon April 27, 2024 at 5:00 am
The FTC has started sending out payments to users of Ring security cameras. Here's why, whether you qualify, and where to look for the check.
- Why Apple Mac Users Should Invest in a VPN: Protecting Your Data and Privacyon April 27, 2024 at 1:09 am
The current era of online security is a scary thing, with users’ privacy being under constant threat. Now, it’s become almost essential to safeguard personal ...
- New iOS 18 AI Security Move Changes The Game For All iPhone Userson April 26, 2024 at 8:07 am
Apple's iOS 18 on the iPhone 16 will be a formidable combination that will offer game-changing features alongside security and privacy. Here's why.
- Ring Users Net $5.6M in Privacy Breach Settlement, Redeem Todayon April 25, 2024 at 11:40 am
Did you have an indoor Ring camera or similar Ring device? There may be a deposit in your PayPal account right now, as part of an Amazon settlement.
- FTC sends $5.6 million in refunds to Ring customers as part of video privacy settlementon April 25, 2024 at 8:18 am
The Federal Trade Commission is sending more than $5.6 million in refunds to consumers as part of a settlement with Amazon-owned Ring, which was charged with failing to protect private video footage f ...
- Dating apps neglect privacy, risk user data: Mozilla researchon April 24, 2024 at 6:02 pm
Recent research by Mozilla suggests an alarming neglect for privacy standards in dating apps, as they gather excessive user data. This could potentially pose a grave online security threat for users, ...
- Some users concerned about privacy, security with dating appson April 24, 2024 at 1:47 pm
Some users who are on popular dating apps are growing concerned with privacy and security when it comes to protecting their information.
- Google’s Privacy Sandbox: What you need to knowon April 24, 2024 at 6:00 am
Learn about what's happening to third-party cookie tracking on Chrome (and identifiers on Android). UPDATED: UK's ICO intervenes. The post Google’s Privacy Sandbox: What you need to know appeared ...
- MetaRouter announces Advanced Consent Enforcement to streamline compliance and user privacyon April 23, 2024 at 11:14 am
MetaRouter provides a configurable enforcement control plane for web event streams that reduces risks associated with data privacy violations.
The Latest Google Headlines on:
User privacy
[google_news title=”” keyword=”user privacy” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]