Fraunhofer AISEC
Company networks are inflexible – they are made up of many components that require a good deal of effort to be connected together.
That’s why networks of the future will be controlled by a central unit. However, this makes them a target for hackers. At CeBIT, Fraunhofer researchers will demonstrate how to protect these future networks.
oday’s company networks comprise hundreds of devices: routers for directing data packets to the right receiver, firewall components for protecting internal networks from the outside world, and network switches. Such networks are extremely inflexible because every component, every router and every switch can carry out only the task it was manufactured for. If the network has to be expanded, the company has to integrate new routers, firewalls or switches and then program them by hand. That’s why experts worldwide have been working on flexible networks of the future for the last five years or so, developing what is known as software-defined networking (SDN). It presents one disadvantage, however; it is susceptible to hacker attacks.
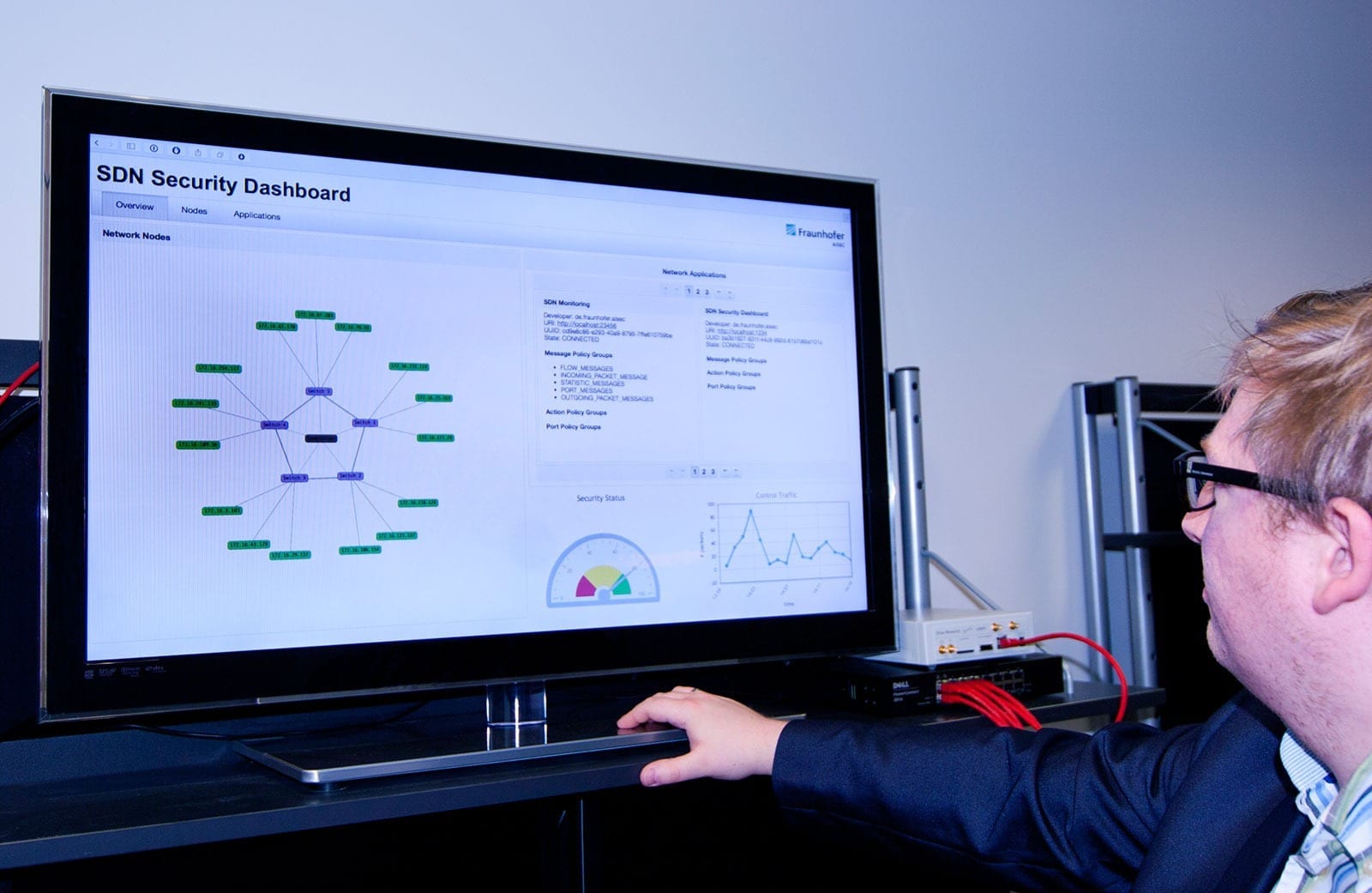
Researchers from the Fraunhofer Institute for Applied and Integrated Security AISEC in Garching, near Munich, will be showing how to make SDN secure at the CeBIT trade fair in Hannover, March 16-20. A demonstrator at the Fraunhofer exhibition stand (Hall 9, Booth E40) will show how SDN and all related components can be monitored. One of these components is visualization software, which displays the network’s individual components and depicts in real time how the various applications are communicating with the controller. “We can show how software influences the behavior of different components using the controller, or, in the case of an attack, how it disrupts them,” says Christian Banse, a security expert at AISEC.
But how exactly does SDN work, and why is it so vulnerable to attack? “In the future, the plan is for a central control unit to tell the many network components what to do. To put it simply, routers, firewalls and switches lose their individual intelligence – they only follow orders from the controller,” says Banse. This makes a network much more flexible, because the controller can allocate completely new tasks to a router or switch that were not intended when the component was manufactured. Plus, the tedious task of manually configuring components during installation is eliminated because components no longer need to be assigned to a specific place in the network – the controller simply uses them as needed at the moment.
The controller is a popular target for hackers
Manufacturers have begun offering the first routers and switches that are SDN-compatible and have the necessary flexibility. “With all the hype surrounding the new adaptability made possible by a central control unit, SDN security has been neglected,” warns Banse. “That’s why we’re developing solutions to make SDN more secure from the outset, before such systems become firmly established.” In the future, networks will be controlled solely by a central controller – Banse sees this as a problem, because it might provide the perfect loophole for attackers to access the entire network.
Read more: Ensuring security for networks of the future
The Latest on: Network security
[google_news title=”” keyword=”Network security” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]
via Google News
The Latest on: Network security
- Corero Network Security and SEMPRE Launch Partnership To Secure the Availability of Critical Infrastructureon May 9, 2024 at 3:59 am
Corero Network Security (LON: CNS) (OTCQB: DDOSF), the distributed denial of service (DDoS) protection specialists, announced a partnership with SEMPRE, a technology company dedicated to securing ...
- Network Security Market to Surpass USD 61.96 billion by 2031 | SkyQuest Technologyon May 9, 2024 at 2:00 am
Westford, USA, May 09, 2024 (GLOBE NEWSWIRE) -- SkyQuest projects that Global Network Security Market will attain a value of USD 61.96 billion by 2031, with a CAGR of 13.20% over the forecast period ...
- The Role of Identity in Network Securityon May 7, 2024 at 5:00 pm
In response to attacks, many security organizations have acquired hundreds of security tools, making detection and analysis difficult. That’s why "identity ...
- Cisco-backed startup Corelight raises $150M to expand network security serviceson May 2, 2024 at 4:54 am
The new funding will enable Corelight to further develop its technology, which transforms network and cloud activity as well as packet capture into evidence that security teams use to proactively hunt ...
- Network security startup Corelight reels in $150Mon April 30, 2024 at 1:54 pm
Corelight Inc., a startup using open-source tools to detect malicious traffic in enterprise networks, today disclosed that it has closed a $150 million Series E funding round.
- Best Practices for Network Securityon April 21, 2024 at 5:00 pm
Many or all of the products here are from our partners that compensate us. It’s how we make money. But our editorial integrity ensures our experts’ opinions aren’t influenced by compensation.
- Preventing Network Security Threats and Vulnerabilitieson April 14, 2024 at 5:00 pm
Potential attacks, software and platform vulnerabilities, malware and misconfiguration issues can pose serious threats to organizations seeking to protect private, confidential or proprietary data.
- Network security in 2024: What has changed in the era of cloud computing, and how to adapton October 31, 2023 at 5:44 pm
As Tufin's Network Security Evangelist, he bridges customers and the marketing and product teams, educating stakeholders on network security technologies, cyber security best practices and Tufin's ...
- CYB 334 Network Securityon September 16, 2023 at 5:02 am
The course addresses topics related to network security. It starts with studying general network vulnerabilities and progresses to using techniques to protect networks. The use of cryptography is ...
via Bing News