An add-on for antivirus software that can scan across a computer network and trap malicious activity missed by the system firewall is being developed by an international team. Details are reported in the International Journal of Electronic Security and Digital Forensics. The research raises the issue that the developers of both operating systems and antivirus software must work more closely together to reduce the burden of malware on computer systems the world over.
The battle between malware authors and security researchers has changed dramatically in the last few years. The purpose behind malware was often for the sake of a prank, to expose vulnerabilities or for the sake of spite. Today, malware is more about stealing sensitive data and exploiting information for fraud, identity theft and other criminal intent. In addition, much malware is aimed at breaking systems through denial-of-service (DoS) attacks in the name of espionage, whether industrial or political or for “hacktivism”, whereby activists prevent legitimate users from accessing a site they see as the enemy to their cause.
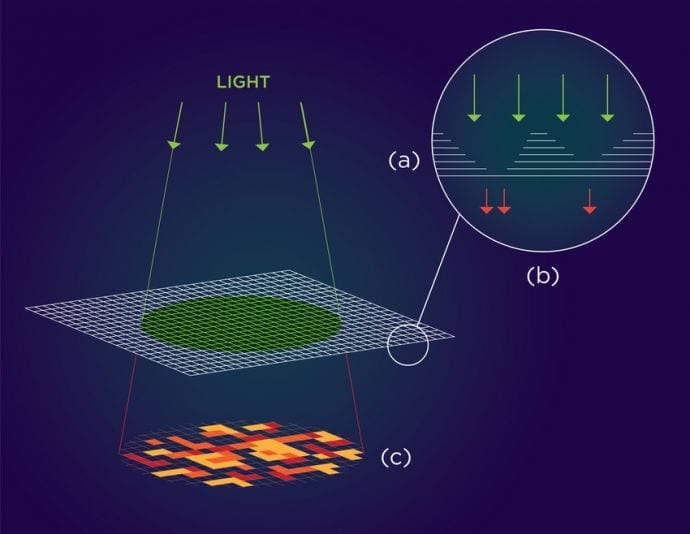
Computer security systems that attempt to thwart the spread of malicious software, malware, often fall down at one of two points of failure. The first being the failure of the network to spot malicious data packets entering the system. The second is that once the network is breached, the antivirus software, which is the last line of network defense fails to identify the software intruder as malicious. Now, researchers in Jordan and the USA have devised an antivirus add-on that allows the AV software to scan the network data as well as applications and so trap malicious activity that the firewall and other defenses that work at the network have missed.
The system devised by computer scientists Mohammed Al-Saleh of Jordan University of Science and Technology in Irbid and Bilal Shebaro of St. Edward’s University, Austin, Texas, side-steps the problem of additional computing overheads placed on a network attempting to detect the spread of malware that may well be encrypted and avoids the issue of antivirus software becoming out-of-date the instant new malware is written and uploaded and the inevitable vulnerability that occurs during the AV scanning process.
Read more: Low-cost malware detection
The Latest on: Malware detection
[google_news title=”” keyword=”malware detection” num_posts=”10″ blurb_length=”0″ show_thumb=”left”]
via Google News
The Latest on: Malware detection
- Google Update Warning Issued For Millions Of Android Userson April 26, 2024 at 1:00 pm
Another warning has just been issued for the millions of Android users likely to click on links to apps and updates from within messages and emails. Just as we saw in February, a fake Chrome update is ...
- Powerful ‘Brokewell’ Android Trojan Allows Attackers to Takeover Deviceson April 26, 2024 at 12:36 pm
A new Android trojan named Brokewell can steal user’s sensitive information and allows attackers to take over devices.
- Brokewell Android malware can completely take over your phoneon April 26, 2024 at 3:38 am
Security researchers at Threat Fabric have discovered a new Android malware that can capture everything you do on your phone. Dubbed Brokewell, the malware can read all touch inputs, app launches, ...
- Malware Analysis Market CAGR of 31%, Ethnography Techniques Revealing the Unconscious Factors Shaping Consumer Behavioron April 25, 2024 at 4:20 pm
Global Malware Analysis Market is valued at approximately USD 3 billion in 2019 and is anticipated to grow with a healthy growth rate of more than 31% over the forecast period 2020-2027. Malware ...
- New Brokewell malware takes over Android devices, steals dataon April 25, 2024 at 3:00 am
Security researchers have discovered a new Android banking trojan they named Brokewell that can capture every event on the device, from touches and information displayed to text input and the ...
- Russian state-sponsored hacker used GooseEgg malware to steal Windows credentialson April 23, 2024 at 4:28 am
A now-patched Windows Print Spooler flaw was used by Forest Blizzard to drop the privilege-elevating malware for credential stealing and persistence.
- 10 Types of Malware and How to Spot Themon April 22, 2024 at 11:53 am
Your guide to the best in personal financial products such as credit cards, mortgages, bank accounts, and brokerages.
- OfflRouter Malware Evades Detection in Ukraine for Almost a Decadeon April 18, 2024 at 9:36 pm
Ukrainian government networks have been compromised by the OfflRouter malware since 2015. This malware is causing sensitive documents to be exposed.
- Sneaky Android Malware Evades Detection – Is Your Phone Safe?on April 18, 2024 at 10:32 am
Another day, another trojan is on the loose, targeting Android users. This time, the ‘SoumniBot’ was found, and some pretty clever tricks were used to avoid detection. Currently, it’s mainly targeting ...
- Kaspersky Study: Devices Infected With Data-Stealing Malware Increased by 7 Times Since 2020on April 18, 2024 at 9:26 am
The number of devices infected with data-stealing malware has increased seven times since 2020, according to new research from Kaspersky.
via Bing News