Researchers develop an algorithm that defends against side-channel attacks on hardware Researchers at the University of Cincinnati developed an algorithm that safeguards hardware from attack... Read more
Researchers at the University of York have shown that a new quantum-based procedure for distributing secure information along communication lines could be successful in preventing serious se... Read more
A power cut in western Ukraine last month was caused by a type of hacking known as “spear-phishing”, says the US Department of Homeland Security (DHS). The attack caused a blacko... Read more
Over the last four years, foreign hackers have stolen source code and blueprints to the oil and water pipelines and power grid of the United States and have infiltrated the Department of Ene... Read more
In 2011, two Dutch hackers in their early 20s made a target list of 100 high-tech companies they would try to hack. Soon, they had found security vulnerabilities in Facebook, Google, Apple,... Read more
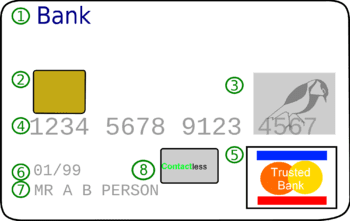
Black and gray markets for computer hacking tools, services and byproducts such as stolen credit card numbers continue to expand, creating an increasing threat to businesses, governments and... Read more